Exam Code: 312-50v11 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Certified Ethical Hacker Exam (CEH v11)
Certification Provider: EC-Council
Free Today! Guaranteed Training- Pass 312-50v11 Exam.
Check 312-50v11 free dumps before getting the full version:
NEW QUESTION 1
An attacker, using a rogue wireless AP, performed an MITM attack and injected an HTML code to embed a malicious applet in all HTTP connections.
When users accessed any page, the applet ran and exploited many machines. Which one of the following tools the hacker probably used to inject HTML code?
- A. Wireshark
- B. Ettercap
- C. Aircrack-ng
- D. Tcpdump
Answer: B
NEW QUESTION 2
This is an attack that takes advantage of a web site vulnerability in which the site displays content that includes un-sanitized user-provided data.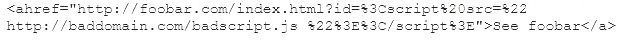
What is this attack?
- A. Cross-site-scripting attack
- B. SQL Injection
- C. URL Traversal attack
- D. Buffer Overflow attack
Answer: A
NEW QUESTION 3
John is an incident handler at a financial institution. His steps in a recent incident are not up to the standards of the company. John frequently forgets some steps and procedures while handling responses as they are very stressful to perform. Which of the following actions should John take to overcome this problem with the least administrative effort?
- A. Create an incident checklist.
- B. Select someone else to check the procedures.
- C. Increase his technical skills.
- D. Read the incident manual every time it occurs.
Answer: C
NEW QUESTION 4
To determine if a software program properly handles a wide range of invalid input, a form of automated testing can be used to randomly generate invalid input in an attempt to crash the program.
What term is commonly used when referring to this type of testing?
- A. Randomizing
- B. Bounding
- C. Mutating
- D. Fuzzing
Answer: D
NEW QUESTION 5
Steve, a scientist who works in a governmental security agency, developed a technological solution to identify people based on walking patterns and implemented this approach to a physical control access.
A camera captures people walking and identifies the individuals using Steve’s approach.
After that, people must approximate their RFID badges. Both the identifications are required to open the door. In this case, we can say:
- A. Although the approach has two phases, it actually implements just one authentication factor
- B. The solution implements the two authentication factors: physical object and physical characteristic
- C. The solution will have a high level of false positives
- D. Biological motion cannot be used to identify people
Answer: B
NEW QUESTION 6
Study the snort rule given below: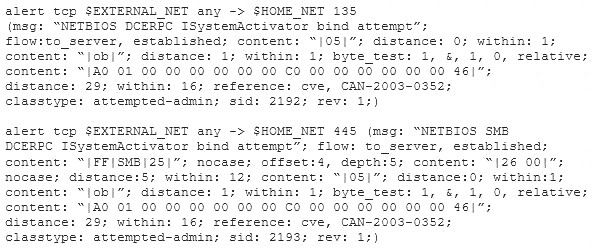
From the options below, choose the exploit against which this rule applies.
- A. WebDav
- B. SQL Slammer
- C. MS Blaster
- D. MyDoom
Answer: C
NEW QUESTION 7
Switches maintain a CAM Table that maps individual MAC addresses on the network to physical ports on the switch.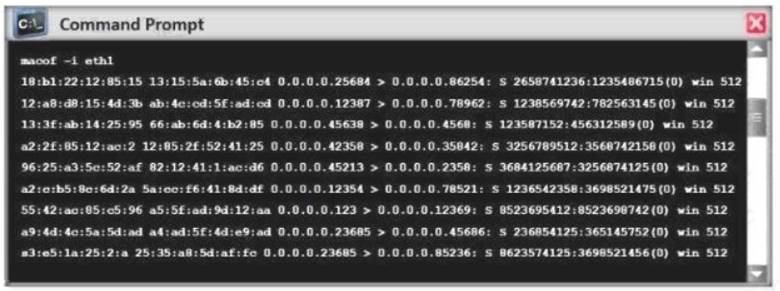
In MAC flooding attack, a switch is fed with many Ethernet frames, each containing different source MAC addresses, by the attacker. Switches have a limited memory for mapping various MAC addresses to physical ports. What happens when the CAM table becomes full?
- A. Switch then acts as hub by broadcasting packets to all machines on the network
- B. The CAM overflow table will cause the switch to crash causing Denial of Service
- C. The switch replaces outgoing frame switch factory default MAC address of FF:FF:FF:FF:FF:FF
- D. Every packet is dropped and the switch sends out SNMP alerts to the IDS port
Answer: A
NEW QUESTION 8
Which of the following Linux commands will resolve a domain name into IP address?
- A. >host-t a hackeddomain.com
- B. >host-t ns hackeddomain.com
- C. >host -t soa hackeddomain.com
- D. >host -t AXFR hackeddomain.com
Answer: A
NEW QUESTION 9
Elliot is in the process of exploiting a web application that uses SQL as a back-end database. He’s determined that the application is vulnerable to SQL injection, and has introduced conditional timing delays into injected queries to determine whether they are successful. What type of SQL injection is Elliot most likely performing?
- A. Error-based SQL injection
- B. Blind SQL injection
- C. Union-based SQL injection
- D. NoSQL injection
Answer: B
NEW QUESTION 10
What do Trinoo, TFN2k, WinTrinoo, T-Sight, and Stracheldraht have in common?
- A. All are hacking tools developed by the legion of doom
- B. All are tools that can be used not only by hackers, but also security personnel
- C. All are DDOS tools
- D. All are tools that are only effective against Windows
- E. All are tools that are only effective against Linux
Answer: C
NEW QUESTION 11
What two conditions must a digital signature meet?
- A. Has to be the same number of characters as a physical signature and must be unique.
- B. Has to be unforgeable, and has to be authentic.
- C. Must be unique and have special characters.
- D. Has to be legible and neat.
Answer: B
NEW QUESTION 12
A network admin contacts you. He is concerned that ARP spoofing or poisoning might occur on his network. What are some things he can do to prevent it? Select the best answers.
- A. Use port security on his switches.
- B. Use a tool like ARPwatch to monitor for strange ARP activity.
- C. Use a firewall between all LAN segments.
- D. If you have a small network, use static ARP entries.
- E. Use only static IP addresses on all PC's.
Answer: ABD
NEW QUESTION 13
The following is an entry captured by a network IDS. You are assigned the task of analyzing this entry. You notice the value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is attempting a buffer overflow attack.
You also notice "/bin/sh" in the ASCII part of the output. As an analyst what would you conclude about the attack?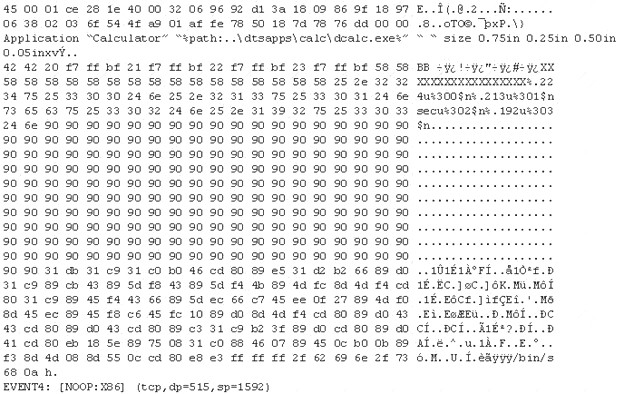
- A. The buffer overflow attack has been neutralized by the IDS
- B. The attacker is creating a directory on the compromised machine
- C. The attacker is attempting a buffer overflow attack and has succeeded
- D. The attacker is attempting an exploit that launches a command-line shell
Answer: D
NEW QUESTION 14
Null sessions are un-authenticated connections (not using a username or password.) to an NT or 2000 system. Which TCP and UDP ports must you filter to check null sessions on your network?
- A. 137 and 139
- B. 137 and 443
- C. 139 and 443
- D. 139 and 445
Answer: D
NEW QUESTION 15
You are performing a penetration test for a client and have gained shell access to a Windows machine on the internal network. You intend to retrieve all DNS records for the internal domain, if the DNS server is at 192.168.10.2 and the domain name is abccorp.local, what command would you type at the nslookup prompt to attempt a zone transfer?
- A. list server=192.168.10.2 type=all
- B. is-d abccorp.local
- C. Iserver 192.168.10.2-t all
- D. List domain=Abccorp.local type=zone
Answer: B
NEW QUESTION 16
Tess King is using the nslookup command to craft queries to list all DNS information (such as Name Servers, host names, MX records, CNAME records, glue records (delegation for child Domains), zone serial number, TimeToLive (TTL) records, etc) for a Domain.
What do you think Tess King is trying to accomplish? Select the best answer.
- A. A zone harvesting
- B. A zone transfer
- C. A zone update
- D. A zone estimate
Answer: B
NEW QUESTION 17
Bob received this text message on his mobile phone: “Hello, this is Scott Smelby from the Yahoo Bank. Kindly contact me for a vital transaction on: scottsmelby@yahoo.com”. Which statement below is true?
- A. This is a scam as everybody can get a @yahoo address, not the Yahoo customer service employees.
- B. This is a scam because Bob does not know Scott.
- C. Bob should write to scottmelby@yahoo.com to verify the identity of Scott.
- D. This is probably a legitimate message as it comes from a respectable organization.
Answer: A
NEW QUESTION 18
When you are getting information about a web server, it is very important to know the HTTP Methods (GET, POST, HEAD, PUT, DELETE, TRACE) that are available because there are two critical methods (PUT and DELETE). PUT can upload a file to the server and DELETE can delete a file from the server. You can detect all these methods (GET, POST, HEAD, DELETE, PUT, TRACE) using NMAP script engine. What Nmap script will help you with this task?
- A. http-methods
- B. http enum
- C. http-headers
- D. http-git
Answer: A
NEW QUESTION 19
A company’s security policy states that all Web browsers must automatically delete their HTTP browser cookies upon terminating. What sort of security breach is this policy attempting to mitigate?
- A. Attempts by attackers to access the user and password information stored in the company’s SQL database.
- B. Attempts by attackers to access Web sites that trust the Web browser user by stealing the user’s authentication credentials.
- C. Attempts by attackers to access password stored on the user’s computer without the user’s knowledge.
- D. Attempts by attackers to determine the user’s Web browser usage patterns, including when sites were visited and for how long.
Answer: B
NEW QUESTION 20
Suppose your company has just passed a security risk assessment exercise. The results display that the risk of the breach in the main company application is 50%. Security staff has taken some measures and
implemented the necessary controls. After that, another security risk assessment was performed showing that risk has decreased to 10%. The risk threshold for the application is 20%. Which of the following risk decisions will be the best for the project in terms of its successful continuation with the most business profit?
- A. Accept the risk
- B. Introduce more controls to bring risk to 0%
- C. Mitigate the risk
- D. Avoid the risk
Answer: A
NEW QUESTION 21
Which of the following are well known password-cracking programs?
- A. L0phtcrack
- B. NetCat
- C. Jack the Ripper
- D. Netbus
- E. John the Ripper
Answer: AE
NEW QUESTION 22
Although FTP traffic is not encrypted by default, which layer 3 protocol would allow for end-to-end encryption of the connection?
- A. SFTP
- B. Ipsec
- C. SSL
- D. FTPS
Answer: B
NEW QUESTION 23
......
Thanks for reading the newest 312-50v11 exam dumps! We recommend you to try the PREMIUM Thedumpscentre.com 312-50v11 dumps in VCE and PDF here: https://www.thedumpscentre.com/312-50v11-dumps/ (254 Q&As Dumps)