It is impossible to pass IIA IIA-CIA-Part3 exam without any help in the short term. Come to Actualtests soon and find the most advanced, correct and guaranteed IIA IIA-CIA-Part3 practice questions. You will get a surprising result by our Improved Certified Internal Auditor - Part 3, Business Analysis and Information Technology practice guides.
Online IIA IIA-CIA-Part3 free dumps demo Below:
NEW QUESTION 1
Which of the following is an example of a nonfinancial internal failure quality cost?
- A. Decreasing gross profit margins over time.
- B. Foregone contribution margin on lost sales.
- C. Defective units shipped to customers.
- D. Excessive time to convert raw materials into finished goods.
Answer: D
NEW QUESTION 2
Which of the following techniques is the most relevant when an internal auditor conducts a valuation of an organization's physical assets?
- A. Observation.
- B. Inspection.
- C. Original cost.
- D. Vouching.
Answer: B
NEW QUESTION 3
When assessing the adequacy of a risk mitigation strategy, an internal auditor should consider which of the following?
* 1. Management’s tolerance for specific risks.
* 2. The cost versus benefit of implementing a control.
* 3. Whether a control can mitigate multiple risks.
* 4. The ability to test the effectiveness of the control.
- A. 1, 2, and 3
- B. 1, 2, and 4
- C. 1, 3, and 4
- D. 2, 3, and 4
Answer: C
NEW QUESTION 4
According to IIA guidance, which of the following is a primary component of a network security strategy?
- A. Application input controls
- B. Firewall controls.
- C. Transmission encryption controls
- D. Change management controls
Answer: B
NEW QUESTION 5
A department purchased one copy of a software program for internal use. The manager of the department installed the program on an office computer and then made two complete copies of the original software.
Copy 1 was solely for backup purposes.
Copy 2 was for use by another member of the department.
In terms of software licenses and copyright law, which of the following is correct?
- A. Both copies are legal.
- B. Only copy 1 is legal.
- C. Only copy 2 is legal.
- D. Neither copy is legal.
Answer: B
NEW QUESTION 6
Preferred stock is less risky for investors than is common stock because:
- A. Common stock pays dividends as a stated percentage of face value.
- B. Common stock has priority over preferred stock with regard to earnings and assets.
- C. Preferred dividends are usually cumulative.
- D. Preferred stock with no conversion feature has a higher dividend yield than does convertible preferred stock.
Answer: C
NEW QUESTION 7
If a just-in-time purchasing system is successful in reducing the total inventory costs of a manufacturing company, which of the following combinations of cost changes would be most likely to occur?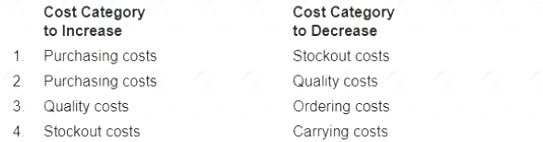
- A. 1
- B. 2
- C. 3
- D. 4
Answer: D
NEW QUESTION 8
The economic order quantity for inventory is higher for an organization that has:
- A. Lower annual unit sales.
- B. Higher fixed inventory ordering costs.
- C. Higher annual carrying costs as a percentage of inventory value.
- D. A higher purchase price per unit of inventory.
Answer: B
NEW QUESTION 9
An organization has instituted a bring-your-own-device (BYOD) work environment Which of the following policies best addresses the increased risk to the organization's network incurred by this environment?
- A. Limit the use of the employee devices for personal use to mitigate the risk of exposure to organizational data.
- B. Ensure that relevant access to key applications is strictly controlled through an approval and review process
- C. Institute detection and authentication controls for all devices used for network connectivity and data storage
- D. Use management software to scan and then prompt patch reminders when devices connect to the network
Answer: D
NEW QUESTION 10
Which of the following is a primary objective of the theory of constraints?
- A. Full or near capacity in processes.
- B. Smooth workflow among processes.
- C. Few or no defects.
- D. Lowered inventory levels.
Answer: A
NEW QUESTION 11
Which of the following controls would be the most effective in preventing the disclosure of an organization s confidential electronic information?
- A. Non-disclosure agreements between the firm and its employees
- B. Logs of user activity within the information system
- C. Two-factor authentication for access into the information system
- D. Limited access to information based on employee duties
Answer: D
NEW QUESTION 12
An organization accumulated the following data for the prior fiscal year: Value of
Percentage of Quarter
Output Produced Cost X
1
$4,750,000 2.9
2
$4,700,000 3.0
3
$4,350,000 3.2
4
$4,000,000 3.5
Based on this data, which of the following describes the value of Cost X in relation to the value of Output Produced?
- A. Cost X is a variable cost.
- B. Cost X is a fixed cost.
- C. Cost X is a semi-fixed cost.
- D. Cost X and the value of Output Produced are unrelated.
Answer: B
NEW QUESTION 13
According to the waterfall cycle approach to systems development, which of the following sequence of events is correct?
- A. Program design, system requirements, software design, analysis, coding, testing, operations.
- B. System requirements, software design, analysis, program design, testing, coding, operations.
- C. System requirements, software design, analysis, program design, coding, testing, operations.
- D. System requirements, analysis, coding, software design, program design, testing, operations.
Answer: C
NEW QUESTION 14
Which of the following authentication controls combines what a user knows with the unique characteristics of the user respectively?
- A. Voice recognition and token.
- B. Password and fingerprint.
- C. Fingerprint and voice recognition
- D. Password and token
Answer: B
NEW QUESTION 15
Division A produces a product with a variable cost of $5 per unit and an allocated fixed cost of S3 per unit The market price of the product is S15 plus 20 percent selling cost. Division B currently purchases this product from an external supplier but is going to purchase it from division A for S18 Which of the following methods of transfer pricing is being used?
- A. Market price.
- B. Negotiation-based.
- C. Full absorption cost
- D. Variable cost
Answer: A
NEW QUESTION 16
Which of the following statements about mentoring is true?
* 1. Mentoring can be used effectively for increasing employee retention
* 2. Mentoring can be used effectively in reducing employees frustration.
* 3. Mentoring can be used effectively for increasing organization communication.
* 4. Mentoring can be used effectively as a short term activity consisting of instruction and training
- A. 1 2. and 3 only.
- B. 1. 2 and 4 only
- C. 1, 3. and 4 only.
- D. 1,2. 3, and 4
Answer: A
NEW QUESTION 17
The board has requested that the internal audit activity be involved in all phases of the organization's outsourcing of its network management. During which of the following stages is the internal auditor most likely to verify that the organization's right-to-audit clause is drafted effectively?
- A. Implementation and transition phase.
- B. Monitoring and reporting phase
- C. Decision-making and business-case phase.
- D. Tendering and contracting phase.
Answer: D
NEW QUESTION 18
......
P.S. Dumps-files.com now are offering 100% pass ensure IIA-CIA-Part3 dumps! All IIA-CIA-Part3 exam questions have been updated with correct answers: https://www.dumps-files.com/files/IIA-CIA-Part3/ (340 New Questions)