Your success in Cisco 350-401 is our sole target and we develop all our 350-401 braindumps in a way that facilitates the attainment of this target. Not only is our 350-401 study material the best you can find, it is also the most detailed and the most updated. 350-401 Practice Exams for Cisco 350-401 are written to the highest standards of technical accuracy.
Cisco 350-401 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1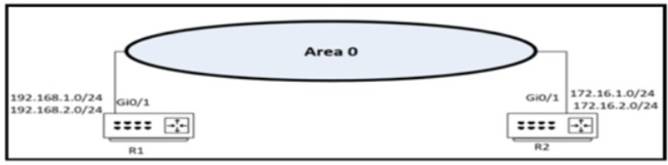
Refer to the exhibit. Which two configurations enable R1 and R2 to advertise routes into OSPF? (Choose two)
A)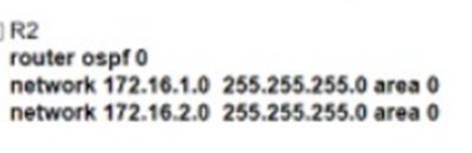
B)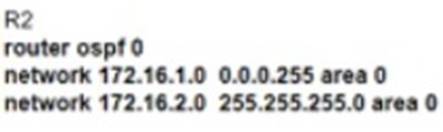
C)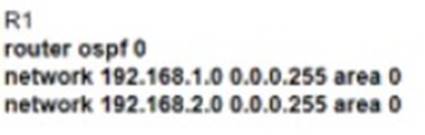
D)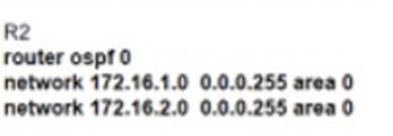
E)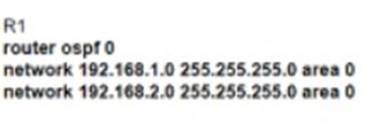
- A. Option A
- B. Option B
- C. Option C
- D. Option DE) Option E
Answer: CD
NEW QUESTION 2
How is traffic classified when using Cisco TrustSec technology?
- A. with the VLAN
- B. with the MAC address
- C. with the IP address
- D. with the security group tag
Answer: D
NEW QUESTION 3
What is a benefit of Cisco TrustSec in a multilayered LAN network design?
- A. Policy or ACLS are nor required.
- B. There is no requirements to run IEEE 802.1X when TrustSec is enabled on a switch port.
- C. Applications flows between hosts on the LAN to remote destinations can be encrypted.
- D. Policy can be applied on a hop-by-hop basis.
Answer: C
NEW QUESTION 4
What are two benefits of virtual switching when compared to hardware switching? (Choose two.)
- A. increased MTU size
- B. hardware independence
- C. VM-level isolation
- D. increased flexibility
- E. extended 802.1Q VLAN range
Answer: CD
NEW QUESTION 5
Which three methods does Cisco DNA Centre use to discover devices? (Choose three)
- A. CDP
- B. SNMP
- C. LLDP
- D. ping
- E. NETCONF
- F. a specified range of IP addresses
Answer: ACF
Explanation: 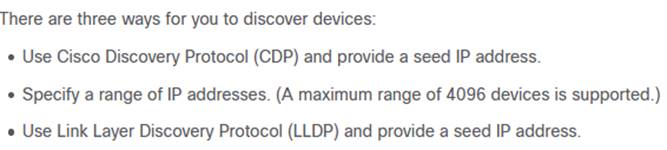
NEW QUESTION 6
Refer to the exhibit.
Which configuration must be applied to the HQ router to set up a GRE tunnel between the HQ and BR routers?
A)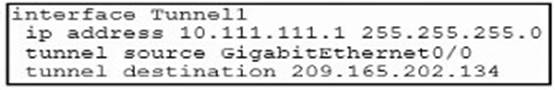
B)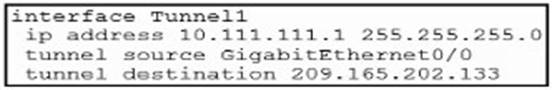
C)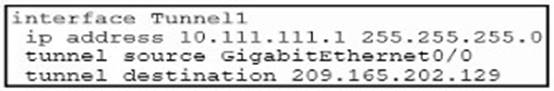
D)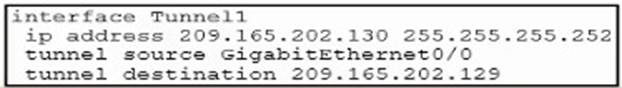
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: A
NEW QUESTION 7
Refer to the exhibit.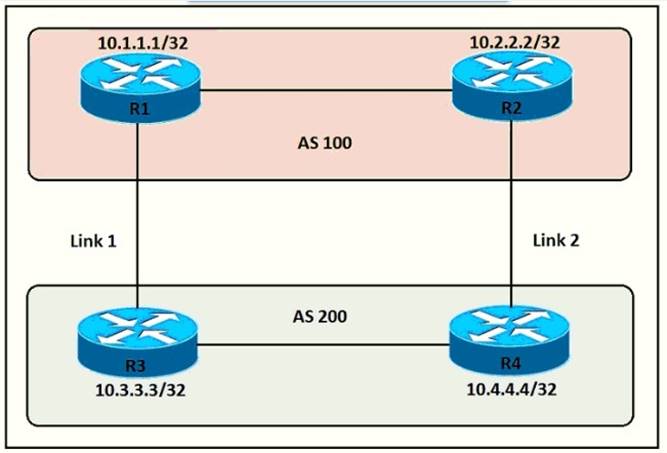
An engineer must ensure that all traffic leaving AS 200 will choose Link 2 as the exit point. Assuming that all BGP neighbor relationships have been formed and that the attributes have not been changed on any of the routers, which configuration accomplish task?
- A. R4(config-router)bgp default local-preference 200
- B. R3(config-router)neighbor 10.1.1.1 weight 200
- C. R3(config-router)bgp default local-preference 200
- D. R4(config-router)nighbor 10.2.2.2 weight 200
Answer: A
Explanation:
Local preference is an indication to the AS about which path has preference to exit
the AS in order to reach a certain network. A path with a higher local preference is preferred. The default value for local preference is 100.
Unlike the weight attribute, which is only relevant to the local router, local preference is an attribute that routers exchange in the same AS. The local preference is set with the “bgp default local-preference value” command.
In this case, both R3 & R4 have exit links but R4 has higher local-preference so R4 will be chosen as the preferred exit point from AS 200.
NEW QUESTION 8
Which two results occur if Cisco DNA Center loses connectivity to devices in the SD- Access fabric? (Choose two)
- A. Cisco DNA Center is unable to collect monitoring data in Assurance.
- B. All devices reload after detecting loss of connection to Cisco DNA Center.
- C. Already connected users are unaffected, but new users cannot connect
- D. Users lose connectivity.
- E. User connectivity is unaffected.
Answer: AE
NEW QUESTION 9
DRAG DROP
Drag and drop the characteristics from the left onto the switching architectures on the right.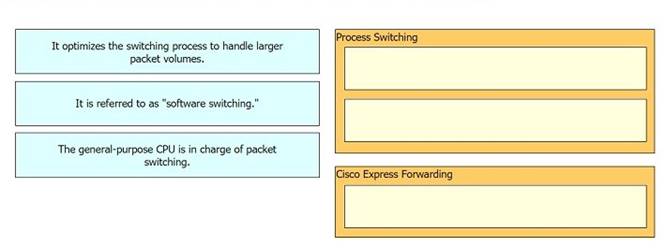
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
How does CEF switching differ from process switching on Cisco devices?
- A. CEF switching saves memory by sorting adjacency tables in dedicate memory on the line cards, and process switching stores all tables in the main memory
- B. CEF switching uses adjacency tables built by the CDP protocol, and process switching uses the routing table
- C. CEF switching uses dedicated hardware processors, and process switching uses the main processor
- D. CEF switching uses proprietary protocol based on IS-IS for MAC address lookup, and process switching uses in MAC address table
Answer: B
Explanation:
Cisco Express Forwarding (CEF) switching is a proprietary form of scalable switching intended to tackle the problems associated with demand caching. With CEF switching, the information which is conventionally stored in a route cache is split up over several data structures. The CEF code is able to maintain these data structures in the Gigabit Route Processor (GRP), and also in slave processors such as the line cards in the 12000 routers. The data structures that provide optimized lookup for efficient packet forwarding include:
✑ The Forwarding Information Base (FIB) table - CEF uses a FIB to make IP destination prefix-based switching decisions. The FIB is conceptually similar to a routing table or information base. It maintains a mirror image of the forwarding information contained in the IP routing table. When routing or topology changes occur in the network, the IP routing table is updated, and these changes are reflected in the FIB. The FIB maintains next-hop address information based on the information in the IP routing table.
Because there is a one-to-one correlation between FIB entries and routing table entries, the FIB contains all known routes and eliminates the need for route cache maintenance that is associated with switching paths such as fast switching and optimum switching.
✑ Adjacency table - Nodes in the network are said to be adjacent if they can reach each other with a single hop across a link layer. In addition to the FIB, CEF uses adjacency tables to prepend Layer 2 addressing information. The adjacency table maintains Layer 2 next-hop addresses for all FIB entries.
CEF can be enabled in one of two modes:
✑ Central CEF mode - When CEF mode is enabled, the CEF FIB and adjacency tables reside on the route processor, and the route processor performs the express forwarding. You can use CEF mode when line cards are not available for CEF switching, or when you need to use features not compatible with distributed CEF switching.
✑ Distributed CEF (dCEF) mode - When dCEF is enabled, line cards maintain identical copies of the FIB and adjacency tables. The line cards can perform the express forwarding by themselves, relieving the main processor - Gigabit Route Processor (GRP) - of involvement in the switching operation. This is the only switching method available on the Cisco 12000 Series Router.
dCEF uses an Inter-Process Communication (IPC) mechanism to ensure synchronization of FIBs and adjacency tables on the route processor and line cards.
For more information about CEF switching, see Cisco Express Forwarding (CEF) White Paper.
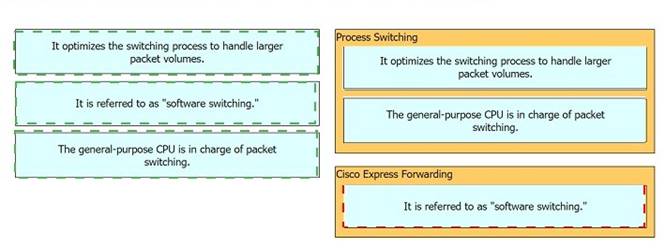
NEW QUESTION 11
Running the script causes the output in the exhibit. Which change to the first line of the script resolves the error?
- A. from ncclient import
- B. import manager
- C. from ncclient import*
- D. import ncclient manager
Answer: C
NEW QUESTION 12
Which configuration restricts the amount of SSH traffic that a router accepts to 100 kbps?
A)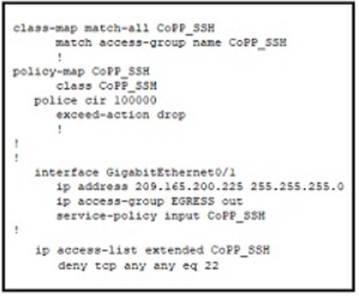
B)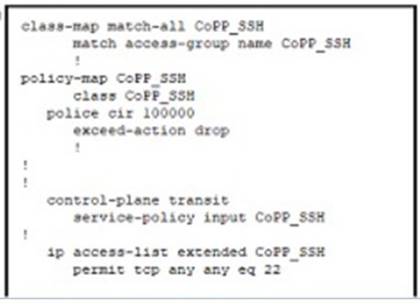
C)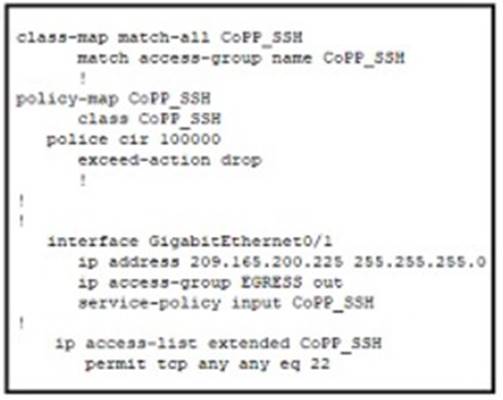
D)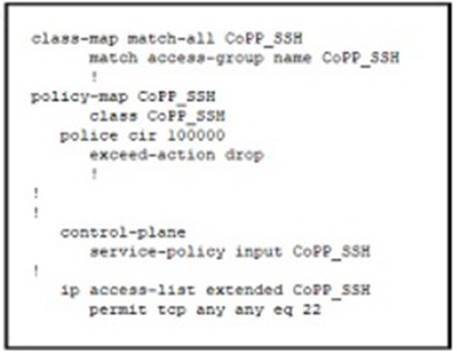
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 13
Which of the following attacks becomes more effective because of global leakages of users' passwords?
- A. Dictionary
- B. Brute-force
- C. Phishing
- D. Deauthentication
Answer: A
Explanation:
This is because a dictionary attack is a type of password cracking attack that uses a list of common or previously leaked passwords to guess the credentials of a user. A dictionary attack becomes more effective because of global leakages of users’ passwords, as the attacker can use the leaked passwords as a source for the dictionary. The source of this answer is the Cisco ENCOR v1.1 course, module 2, lesson 2.3: Implementing Wireless Security.
NEW QUESTION 14
Which two Cisco SD-WAN components exchange OMP information?
- A. vAnaiytlcs
- B. vSmart
- C. WAN Edge
- D. vBond
- E. vManage
Answer: BC
NEW QUESTION 15
A company recently rearranged some users' workspaces and moved several users to different desks. The network administrator receives a report that all of the users who were moved are having connectivity issues. Which of the following is the most likely reason?
- A. Ports are error disabled.
- B. Ports are administratively down.
- C. Ports are having an MDIX issue.
- D. Ports are trunk ports.
Answer: A
Explanation:
This is because ports can become error disabled when they detect certain errors or violations on the network, such as a loop, a security breach, or a duplex mismatch. When a port is error disabled, it shuts down and stops forwarding traffic until it is manually re-enabled by the administrator. The users who were moved to different desks may have plugged their devices into ports that were configured with different settings or security policies than their original ports, and this may have triggered the error disable state. The source of this answer is the Cisco ENCOR v1.1 course, module 3, lesson 3.3: Implementing EtherChannel.
NEW QUESTION 16
A customer requests a network design that supports these requirements:
Which protocol does the design include?
- A. HSRP version 2
- B. VRRP version 2
- C. GLBP
- D. VRRP version 3
Answer: D
NEW QUESTION 17
What does the number in an NTP stratum level represent?
- A. The number of hops it takes to reach the master time server.
- B. The number of hops it takes to reach the authoritative time source.
- C. The amount of offset between the device clock and true time.
- D. The amount of drift between the device clock and true time.
Answer: B
NEW QUESTION 18
What is one benefit of implementing a VSS architecture?
- A. It provides multiple points of management for redundancy and improved support
- B. It uses GLBP to balance traffic between gateways.
- C. It provides a single point of management for improved efficiency.
- D. It uses a single database to manage configuration for multiple switches
Answer: C
Explanation:
Support Virtual Switching System (VSS) to provide resiliency, and increased operational efficiency with a single point of management;
VSS increases operational efficiency by simplifying the network, reducing switch
management overhead by at least 50 percent. – Single configuration file and node to manage. Removes the need to configure redundant switches twice with identical policies.
NEW QUESTION 19
In a three-tier hierarchical campus network design, which action is a design best-practice for the core layer?
- A. provide QoS prioritization services such as marking, queueing, and classification for critical network traffic
- B. provide redundant Layer 3 point-to-point links between the core devices for more predictable and faster convergence
- C. provide advanced network security features such as 802. IX, DHCP snooping, VACLs, and port security
- D. provide redundant aggregation for access layer devices and first-hop redundancy protocols such as VRRP
Answer: B
NEW QUESTION 20
Which DNS lookup does an AP perform when attempting CAPWAP discovery?
- A. CAPWAP-CONTROLLER.Iocal
- B. CISCO-CAPWAP-CONTROLLER.Iocal
- C. CISCO-DNA-CONTROLLER.Iocal
- D. CISCO-CONTROLLER.Iocal
Answer: B
NEW QUESTION 21
......
Recommend!! Get the Full 350-401 dumps in VCE and PDF From Dumps-files.com, Welcome to Download: https://www.dumps-files.com/files/350-401/ (New 188 Q&As Version)