Proper study guides for Leading Cisco Implementing and Operating Cisco Enterprise Network Core Technologies certified begins with Cisco 350-401 preparation products which designed to deliver the Practical 350-401 questions by making you pass the 350-401 test at your first time. Try the free 350-401 demo right now.
Free 350-401 Demo Online For Cisco Certifitcation:
NEW QUESTION 1
In a Cisco Catalyst switch equipped with two supervisor modules an administrator must temporally remove the active supervisor from the chassis to perform hardware maintenance on it. Which mechanism ensure that the active supervisor removal is not disruptive to the network operation?
- A. NSF/NSR
- B. SSO
- C. HSRP
- D. VRRP
Answer: B
NEW QUESTION 2
Which JSON script is properly formatted?
A)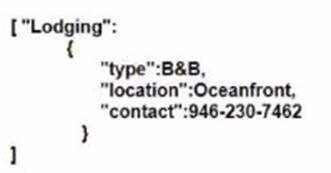
B)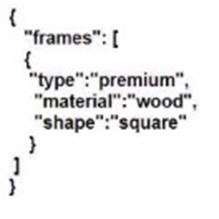
C)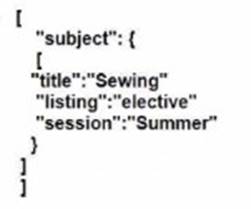
D)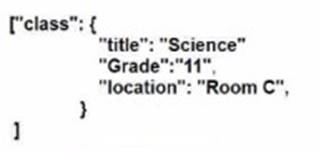
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: A
Explanation:
Option A is the properly formatted JSON script. JSON (JavaScript Object Notation) is a standard text-based format for representing structured data based on JavaScript object syntax. It is commonly used for transmitting data in web applications (e.g., sending some data from the server to the client, so it can be displayed on a web page, or vice versa). The JSON syntax rules are as follows12:
✑ Data is in name/value pairs, separated by commas. A name/value pair consists of a field name (in double quotes), followed by a colon, followed by a value: "name": "value".
✑ Curly braces hold objects. An object can contain multiple name/value pairs: {"name": "value", "name": "value", ...}.
✑ Square brackets hold arrays. An array can contain multiple values, separated by commas: ["value", "value", ...].
✑ Values can be strings (in double quotes), numbers, booleans (true or false), null, objects, or arrays.
Option A follows these rules and is a valid JSON script. It defines an object with four name/value pairs: "name", "age", "hobbies", and "address". The value of "name" is a string, the value of "age" is a number, the value of "hobbies" is an array of strings, and the value of "address" is another object with two name/value pairs: "city" and "country". The object is enclosed in curly braces and the name/value pairs are separated by commas.
Option B is not a valid JSON script because it uses single quotes instead of double quotes for the field names and string values. JSON requires double quotes for strings12.
Option C is not a valid JSON script because it does not use commas to separate the name/value pairs. JSON requires commas to separate the data elements within an object or an array12.
Option D is not a valid JSON script because it uses a semicolon instead of a colon to separate the field name and the value. JSON requires a colon to separate the name and the value in a name/value pair12. References: 1: JSON Introduction, 2: JSON Syntax
NEW QUESTION 3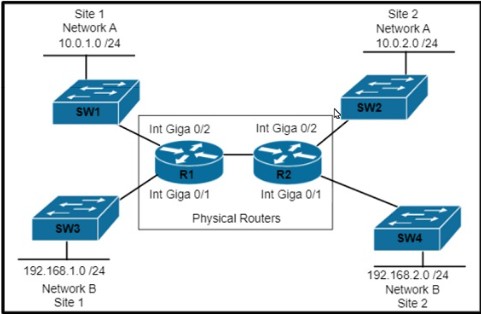
Refer to the exhibit. Which set of commands is required to configure and verify the VRF for Site 1 Network A on router R1?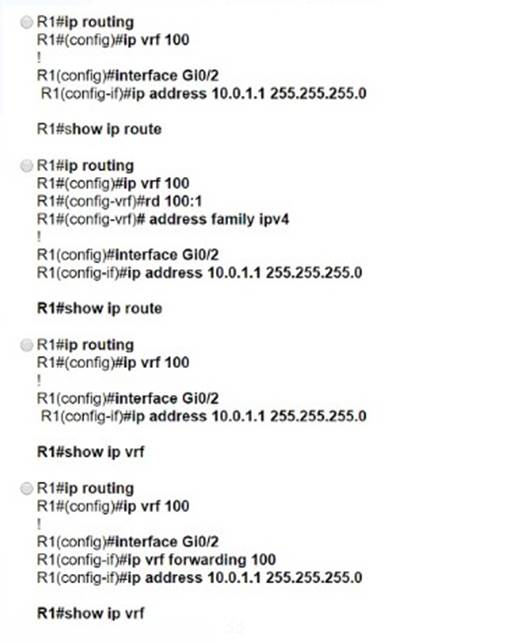
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 4
Refer to the exhibit.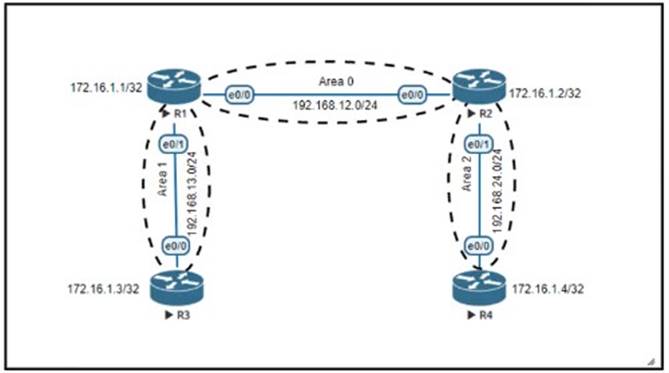
An engineer must create a configuration that prevents R3from receiving the LSA about 172.16.1.4/32.Which configuration set achieves this goal?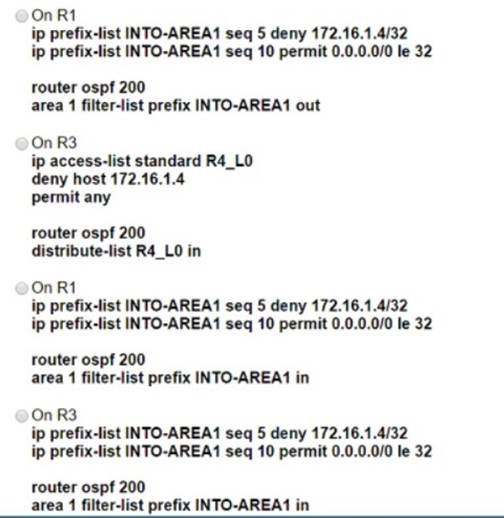
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 5
Which network devices secure API platform?
- A. next-generation intrusion detection systems
- B. Layer 3 transit network devices
- C. content switches
- D. web application firewalls
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/products/collateral/security/advanced-waf-bot- aag.pdf> Cisco® Secure Web Application Firewall (WAF) and bot protection defends your> online presence and ensures that website, mobile applications, and APIs> are secure, protected, and “always on.”
NEW QUESTION 6
What is one fact about Cisco SD-Access wireless network deployments?
- A. The access point is part of the fabric underlay
- B. The WLC is part of the fabric underlay
- C. The access point is part the fabric overlay
- D. The wireless client is part of the fabric overlay
Answer: C
NEW QUESTION 7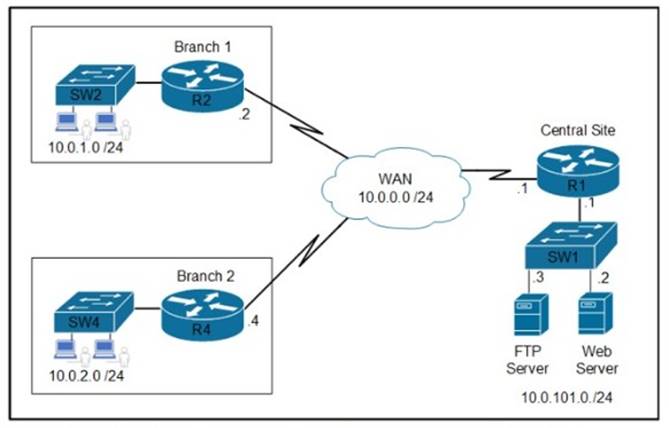
Refer to the exhibit Which two commands are required on route» R1 to block FTP and allow all other traffic from the Branch 2 network’ (Choose two)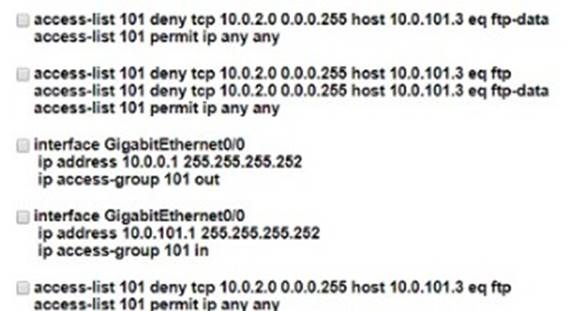
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer: BC
NEW QUESTION 8
Which VXLAN component is used to encapsulate and decapsulate Ethernet frames?
- A. VNI
- B. GRE
- C. VTEP
- D. EVPN
Answer: C
NEW QUESTION 9
DRAG DROP
Drag and drop the REST API authentication methods from the left onto their descriptions on the right.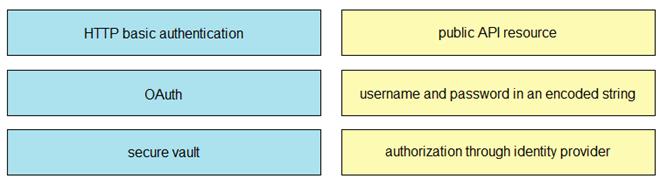
Solution:
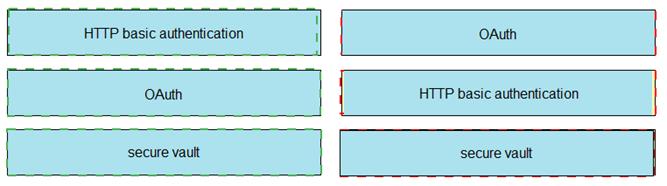
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
Which two methods are used to reduce the AP coverage area? (Choose two)
- A. Reduce channel width from 40 MHz to 20 MHz
- B. Disable 2.4 GHz and use only 5 GHz.
- C. Reduce AP transmit power.
- D. Increase minimum mandatory data rate
- E. Enable Fastlane
Answer: CD
NEW QUESTION 11
A wireless network engineer must configure a WPA2+WPA3 policy with the Personal security type. Which action meets this requirement?
- A. Configure the GCMP256 encryption cipher.
- B. Configure the CCMP256 encryption cipher.
- C. Configure the CCMP128 encryption cipher.
- D. Configure the GCMP128 encryption cipher.
Answer: A
Explanation:
This is because the GCMP256 cipher is the only one that supports both WPA2 and WPA3 with the Personal security type. The GCMP256 cipher provides stronger encryption and authentication than the CCMP ciphers, which are only compatible with WPA2. The source of this answer is the Cisco ENCOR v1.1 course, module 7, lesson 7.2: Implementing WPA2 and WPA3.
NEW QUESTION 12
When using TLS for syslog, which configuration allows for secure and reliable transportation of messages to its default port?
- A. logging host 10.2.3.4 vrf mgmt transport tcp port 6514
- B. logging host 10.2.3.4 vrf mgmt transport udp port 6514
- C. logging host 10.2.3.4 vrf mgmt transport tcp port 514
- D. logging host 10.2.3.4 vrf mgmt transport udp port 514
Answer: A
Explanation:
The TCP port 6514 has been allocated as the default port for syslog over Transport Layer Security (TLS).
Reference: https://tools.ietf.org/html/rfc5425
NEW QUESTION 13
Refer to the exhibit.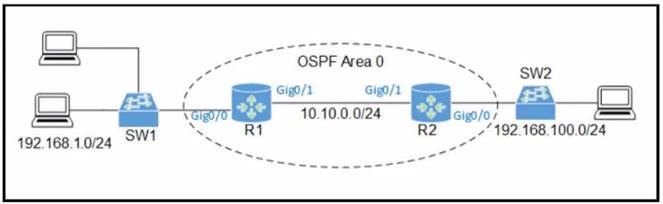
An engineer must allow R1 to advertise the 192 168.1 0/24 network to R2 R1 must perform this action without sending OSPF packets to SW1 Which command set should be applied?
A)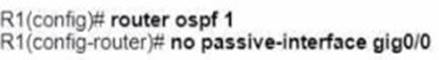
B)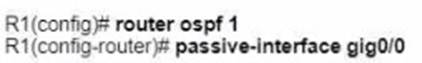
C)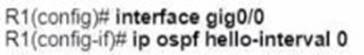
D)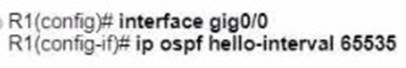
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 14
Refer to the exhibit.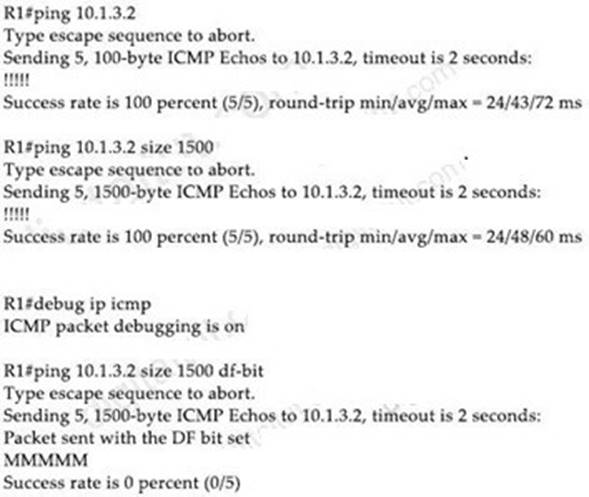
An engineer troubleshoots connectivity issues with an application. Testing is performed from the server gateway, and traffic with the DF bit set is dropped along the path after increasing packet size. Removing the DF bit setting at the gateway prevents the packets from being dropped. What is the cause of this issue?
- A. PMTUD does not work due to ICMP Packet Too Big messages being dropped by an ACL
- B. The remote router drops the traffic due to high CPU load
- C. The server should not set the DF bit in any type of traffic that is sent toward the network
- D. There is a CoPP policy in place protecting the WAN router CPU from this type of traffic
Answer: C
NEW QUESTION 15
Refer to the exhibit.
An engineer must prevent the R6 loopback from getting into Area 2 and Area 3 from Area 0 Which action must the engineer take?
- A. Apply a fitter list inbound on R2 and R9
- B. Apply a filter list outbound on R3 and R7
- C. Apply a filter list outbound on R7 only.
- D. Apply a filter list inbound on R3 and R7
Answer: B
Explanation:
This question asks to prevent route advertised into Area 2 and Area 3 only. It does not ask to prevent route advertised into Area 0 so applying a filter list outbound on R3 and R7 would best fit the requirement.
NEW QUESTION 16
Which measure is used by an NTP server to indicate its closeness to the authoritative time source?
- A. latency
- B. hop count
- C. time zone
- D. stratum
Answer: D
NEW QUESTION 17
A server running Linux is providing support for virtual machines along with DNS and DHCP services for a small business. Which technology does this represent?
- A. container
- B. Type 1 hypervisor
- C. hardware pass-thru
- D. Type 2 hypervisor
Answer: D
Explanation:
In contrast to type 1 hypervisor, a type 2 hypervisor (or hosted hypervisor) runs on top of an operating system and not the physical hardware directly. A big advantage of Type 2 hypervisors is that management console software is not required. Examples of type 2 hypervisor are VMware Workstation (which can run on Windows, Mac and Linux) or Microsoft Virtual PC (only runs on Windows).
NEW QUESTION 18
What is the output of this code?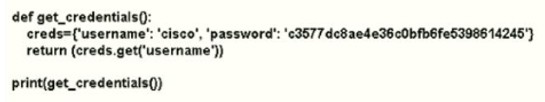
- A. username Cisco
- B. get_credentials
- C. username
- D. CISCO
Answer: D
NEW QUESTION 19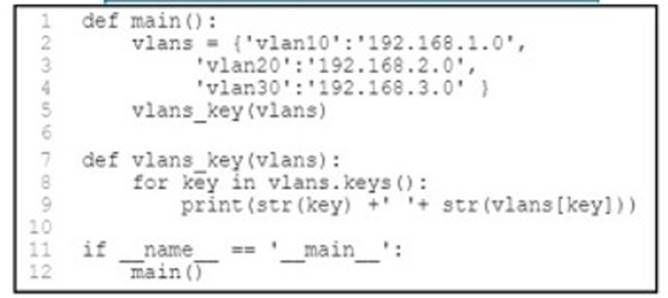
Refer to the exhibit. What is printed to the console when this script is run?
- A. a key-value pair in tuple type
- B. a key-value pair in list type
- C. a key-value pair in string type
- D. an error
Answer: C
NEW QUESTION 20
Which method ensures the confidentiality ot data exchanged over a REST API?
- A. Use the POST method instead of URL-encoded GET to pass parameters.
- B. Encode sensitive data using Base64 encoding.
- C. Deploy digest-based authentication to protect the access to the API.
- D. Use TLS to secure the underlying HTTP session.
Answer: B
NEW QUESTION 21
......
100% Valid and Newest Version 350-401 Questions & Answers shared by Certleader, Get Full Dumps HERE: https://www.certleader.com/350-401-dumps.html (New 188 Q&As)