It is more faster and easier to pass the Cisco 350-401 exam by using Tested Cisco Implementing and Operating Cisco Enterprise Network Core Technologies questuins and answers. Immediate access to the Most up-to-date 350-401 Exam and find the same core area 350-401 questions with professionally verified answers, then PASS your exam with a high score now.
Online Cisco 350-401 free dumps demo Below:
NEW QUESTION 1
Which AP mode allows an engineer to scan configured channels for rogue access points?
- A. sniffer
- B. monitor
- C. bridge
- D. local
Answer: B
NEW QUESTION 2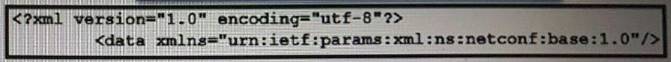
Refer to the exhibit. What does the error message relay to the administrator who is trying to configure a Cisco IOS device?
- A. A NETCONF request was made for a data model that does not exist.
- B. The device received a valid NETCONF request and serviced it without error.
- C. A NETCONF message with valid content based on the YANG data models was made, but the request failed.
- D. The NETCONF running datastore is currently locked.
Answer: A
Explanation:
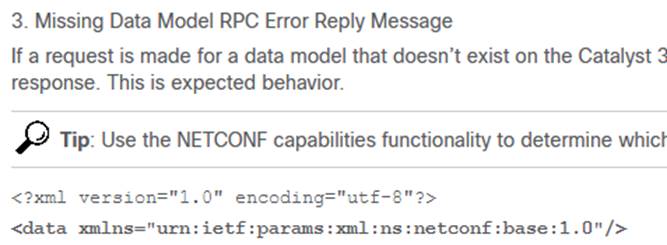
Reference: https://www.cisco.com/c/en/us/support/docs/storage-networking/management/200933-YANG-NETCONF-Configuration-Validation.html
NEW QUESTION 3
An engineer is troubleshooting the Ap join process using DNS. Which FQDN must be resolvable on the network for the access points to successfully register to the WLC?
- A. wlcbostname.domain.com
- B. cisco-capwap-controller.domain.com
- C. ap-manager.domain.com
- D. primary-wlc.domain.com
Answer: B
Explanation:
DNS: If you have configured your DHCP server to provide both option 006 (DNS server address) and option 015 (domain name) information, the AP can obtain WLC addresses from the DNS server. The process works as follows:
* 1. The AP gets its IP address from DHCP with options 6 and 15 configured.
* 2. The AP can obtain the IP address of the DNS server from the DHCP option.
* 3. The AP uses this information to perform a hostname lookup using CISCO-CAPWAP- CONTROLLER.<localdomain>, which resolves to available WLC management interface IP addresses (IPv4 or IPv6, or both).
* 4. The AP can then perform a directed message to associate to responsive WLCs.
To prevent all APs from joining a single controller based on a DNS name resolution, the domain name may vary; this is what is done to dispatch APs to different controllers across the enterprise network, based on different domain names that are configured in their respective DNS scopes.
NEW QUESTION 4
Which design principle slates that a user has no access by default to any resource, and unless a resource is explicitly granted, it should be denied?
- A. least privilege
- B. fail-safe defaults
- C. economy of mechanism
- D. complete mediation
Answer: B
NEW QUESTION 5
DRAG DROP
Drag and drop the code snippets from the bottom onto the blanks in the Python script to print the device model to the screen and write JSON data to a file Not all options are used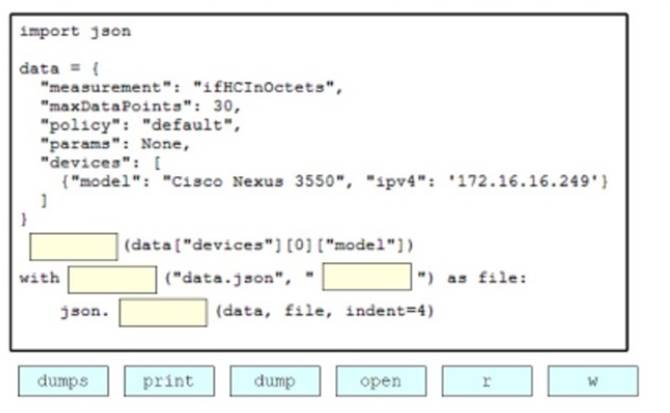
Solution:
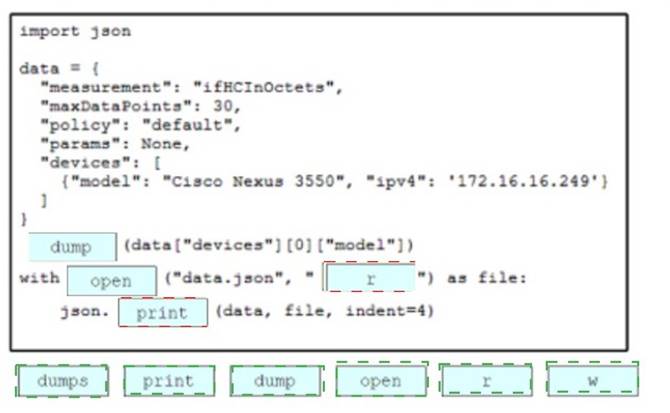
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 6
Which function does a fabric edge node perform in an SD-Access deployment?
- A. Connects the SD-Access fabric to another fabric or external Layer 3 networks
- B. Connects endpoints to the fabric and forwards their traffic
- C. Provides reachability border nodes in the fabric underlay
- D. Encapsulates end-user data traffic into LISP.
Answer: B
Explanation:
There are five basic device roles in the fabric overlay:
+ Control plane node: This node contains the settings, protocols, and mapping tables to provide
the endpoint-to-location (EID-to-RLOC) mapping system for the fabric overlay.
+ Fabric border node: This fabric device (for example, core layer device) connects external Layer
3 networks to the SDA fabric.
+ Fabric edge node: This fabric device (for example, access or distribution layer device) connects
wired endpoints to the SDA fabric.
+ Fabric WLAN controller (WLC): This fabric device connects APs and wireless endpoints to the
SDA fabric.
+ Intermediate nodes: These are intermediate routers or extended switches that do not provide
any sort of SD-Access fabric role other than underlay services.
NEW QUESTION 7
Refer the exhibit.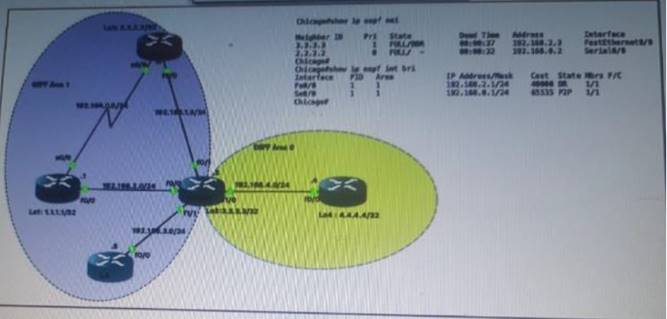
Which router is the designated router on the segment 192.168.0.0/24?
- A. This segment has no designated router because it is a nonbroadcast network type.
- B. This segment has no designated router because it is a p2p network type.
- C. Router Chicago because it has a lower router ID
- D. Router NewYork because it has a higher router ID
Answer: B
NEW QUESTION 8
If a client's radio device receives a signal strength of -67 dBm and the noise floor is -85 dBm, what is the SNR value?
- A. 15 dB
- B. 16 dB
- C. 18 dB
- D. 20 dB
Answer: C
NEW QUESTION 9
DRAG DROP
Drag and drop characteristics of PIM dense mode from the left to the right.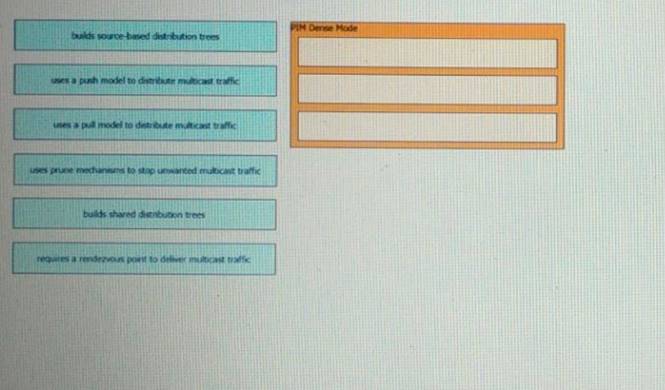
Solution:
PIM-DM supports only source trees – that is, (S,G) entries–and cannot be used to build a shared distribution tree.
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
What is the wireless received signal strength indicator?
- A. The value given to the strength of the wireless signal received compared to the noise level
- B. The value of how strong the wireless signal Is leaving the antenna using transmit power, cable loss, and antenna gain
- C. The value of how much wireless signal is lost over a defined amount of distance
- D. The value of how strong a tireless signal is receded, measured in dBm
Answer: D
Explanation:
RSSI, or “Received Signal Strength Indicator,” is a measurement of how well your device can hear a signal from an access point or router. It’s a value that is useful for determining if you have enough signal to get a good wireless connection.
This value is measured in decibels (dBm) from 0 (zero) to -120 (minus 120). The closer to 0 (zero) the stronger the signal is which means it’s better, typically voice networks require a - 65db or better signal level while a data network needs -80db or better.
NEW QUESTION 11
Refer to the exhibit.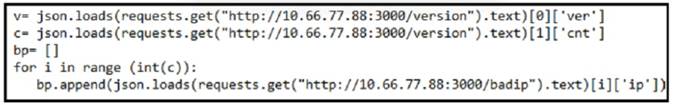
What is achieved by this Python script?
- A. It counts JSON data from a website.
- B. It loads JSON data into an HTTP request.
- C. It reads JSON data into a formatted list.
- D. It converts JSON data to an HTML document.
Answer: B
NEW QUESTION 12
Refer the exhibit.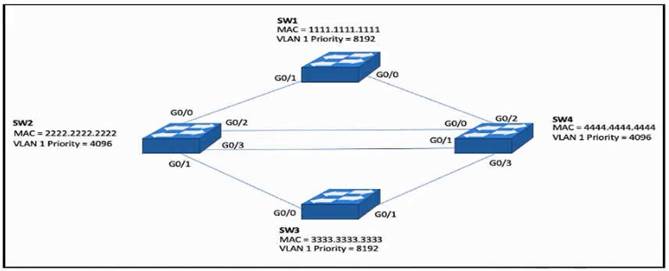
Which configuration elects SW4 as the root bridge for VLAN 1 and puts G0/2 on SW2 into a blocking state?
A)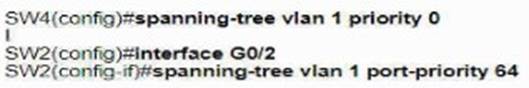
B)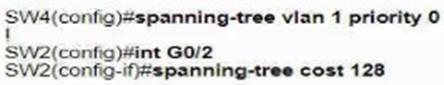
C)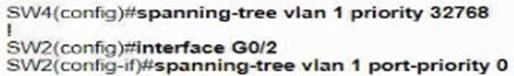
D)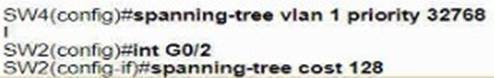
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 13
What is an emulated machine that has dedicated compute memory, and storage resources and a fully installed operating system?
- A. Container
- B. Mainframe
- C. Host
- D. virtual machine
Answer: B
NEW QUESTION 14
What is the result of applying this access control list?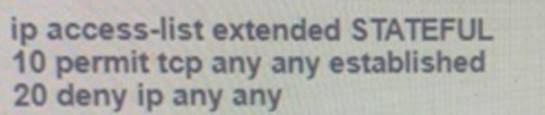
- A. TCP traffic with the URG bit set is allowed
- B. TCP traffic with the SYN bit set is allowed
- C. TCP traffic with the ACK bit set is allowed
- D. TCP traffic with the DF bit set is allowed
Answer: C
NEW QUESTION 15
If AP power level is increased from 25 mW to 100 mW. what is the power difference in dBm?
- A. 6 dBm
- B. 14 dBm
- C. 17 dBm
- D. 20 dBm
Answer: D
NEW QUESTION 16
SIMULATION
Simulation 07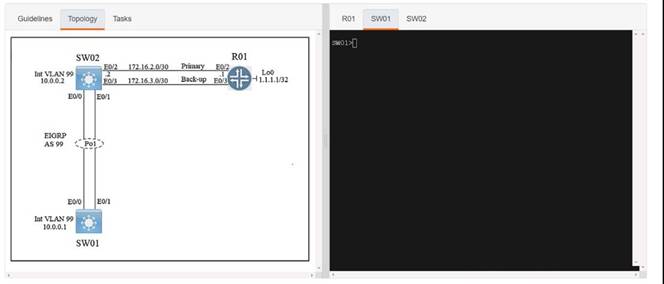
Solution:
Sw1 Config t Archive Log config
Logging enable Notify syslog
R1
Config t
Ip flow-top-talkers
Match source address 172.16.2.1/30 Int et0/2
Ip flow ingress Copy run start
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 17
Where is radio resource management performed in a cisco SD-access wireless solution?
- A. DNA Center
- B. control plane node
- C. wireless controller
- D. Cisco CMX
Answer: C
Explanation:
Fabric wireless controllers manage and control the fabric-mode APs using the same general model as the traditional local-mode controllers which offers the same operational advantages such as mobility control and radio resource management. A significant difference is that client traffic from wireless endpoints is not tunnelled from the APs to the wireless controller. Instead, communication from wireless clients is encapsulated in VXLAN by the fabric APs which build a tunnel to their first-hop fabric edge node. Wireless traffic it tunneled to the edge nodes as the edge nodes provide fabric
services such as the Layer 3 Anycast Gateway, policy, and traffic enforcement. https://www.cisco.com/c/en/us/td/docs/solutions/CVD/Campus/cisco-sda-design-guide.html
NEW QUESTION 18
Which NGFW mode block flows crossing the firewall?
- A. Passive
- B. Tap
- C. Inline tap
- D. Inline
Answer: D
Explanation:
Firepower Threat Defense (FTD) provides six interface modes which are: Routed, Switched, Inline Pair, Inline Pair with Tap, Passive, Passive (ERSPAN).When Inline Pair Mode is in use, packets can be blocked since they are processed inline When you use Inline Pair mode, the packet goes mainly through the FTD Snort engine When Tap Mode is enabled, a copy of the packet is inspected and dropped internally while the actual traffic goes through FTD unmodified
NEW QUESTION 19
Refer to the exhibit.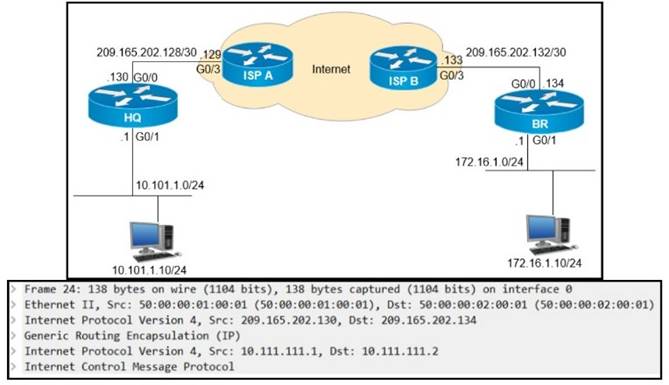
A GRE tunnel has been created between HO and BR routers. What is the tunnel IP on the HQ router?
- A. 10.111.111.1
- B. 10.111.111.2
- C. 209.165.202.130
- D. 209.165.202.134
Answer: A
NEW QUESTION 20
Which access control feature does MAB provide?
- A. user access based on IP address
- B. allows devices to bypass authenticate*
- C. network access based on the physical address of a device
- D. simultaneous user and device authentication
Answer: C
NEW QUESTION 21
......
P.S. Certleader now are offering 100% pass ensure 350-401 dumps! All 350-401 exam questions have been updated with correct answers: https://www.certleader.com/350-401-dumps.html (188 New Questions)