It is impossible to pass Cisco 350-401 exam without any help in the short term. Come to Examcollection soon and find the most advanced, correct and guaranteed Cisco 350-401 practice questions. You will get a surprising result by our Improve Implementing and Operating Cisco Enterprise Network Core Technologies practice guides.
Cisco 350-401 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which three resources must the hypervisor make available to the virtual machines? (Choose three)
- A. memory
- B. bandwidth
- C. IP address
- D. processor
- E. storage
- F. secure access
Answer: ADE
NEW QUESTION 2
A technician needs to find the MAC address of a connecting router. Which of the following commands should the technician use?
- A. arp
- B. traceroute
- C. nslookup
- D. ping
Answer: A
Explanation:
This is because the arp command is used to display or manipulate the Address Resolution Protocol (ARP) cache, which is a table that maps IP addresses to MAC addresses. The arp command can show the MAC address of a connecting router by using the -a option, which displays the current ARP entries. For example, arp -a 192.168.1.1 will show the MAC address of the router with the IP address 192.168.1.1. The source of this answer is the Cisco ENCOR v1.1 course, module 3, lesson 3.1: Implementing IPv4 and IPv6 Addressing.
NEW QUESTION 3
Refer to the exhibit.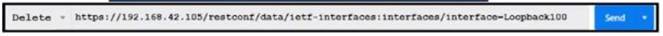
What does the response "204 No Content mean for the REST API request?
- A. Interface toopback 100 is not removed from the configuration.
- B. Interface toopback 100 is not found in the configuration.
- C. Interface toopback 100 is removed from the configuration.
- D. The DELETE method is not supported.
Answer: C
Explanation:
This is because the response “204 No Content” means that the REST API request was successful, but there is no content to return. The request was a DELETE method, which is used to remove a resource from the server. The resource in this case was the interface loopback 100, which was deleted from the configuration of the device. The source of this answer is the Cisco ENCOR v1.1 course, module 8, lesson 8.4: Implementing REST API.
NEW QUESTION 4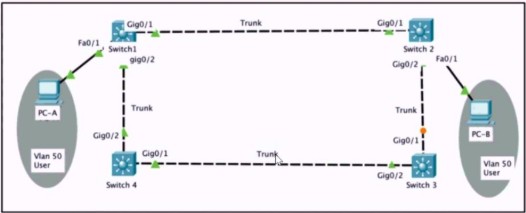
Refer to the exhibit. Rapid PVST+ is enabled on all switches. Which command set must be configured on switch1 to achieve the following results on port fa0/1?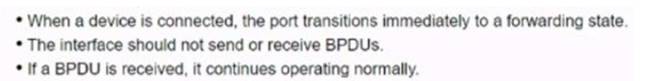
A)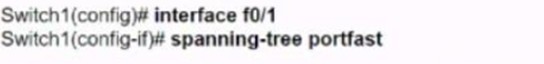
B)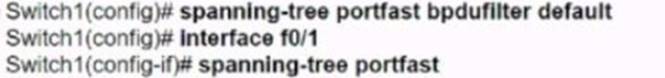
C)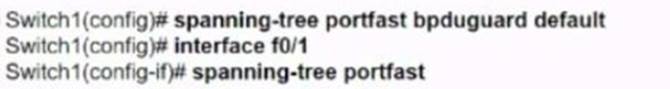
D)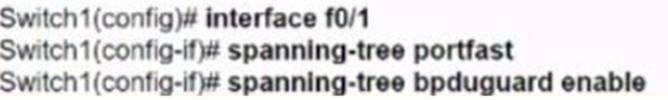
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 5
Refer to the exhibit.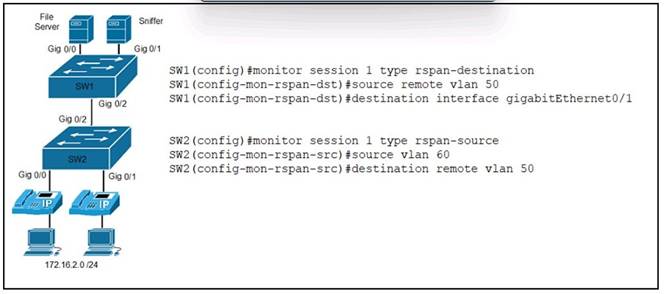
An engineer must send the 172.16.2.0 /24 user traffic to a packet capture tool to troubleshoot an issue. Which action completes the configuration?
- A. Encrypt the traffic between the users and the monitoring servers.
- B. Disable the spanning tree protocol on the monitoring server VLAN.
- C. Enable the Cisco Discovery Protocol on the server interfaces.
- D. Define the remote span VLAN on SW1 and SW2.
Answer: D
Explanation:
This is because the remote span VLAN is used to transport the mirrored traffic from the source switch to the destination switch, where the monitoring server is connected. The remote span VLAN must be defined on both switches and must not be used for any other purpose. The source of this answer is the Cisco ENCOR v1.1 course, module 6, lesson 6.2: Implementing SPAN, RSPAN, and ERSPAN.
NEW QUESTION 6
Which deployment option of Cisco NGFW provides scalability?
- A. tap
- B. clustering
- C. inline tap
- D. high availability
Answer: B
Explanation:
Clustering lets you group multiple Firepower Threat Defense (FTD) units together as a single logical device. Clustering is only supported for the FTD device on the Firepower 9300 and the Firepower 4100 series. A cluster provides all the convenience of a single device (management, integration into a network) while achieving the increased throughput and redundancy of multiple devices.}
NEW QUESTION 7
Which two items are found in YANG data models? (Choose two.)
- A. HTTP return codes
- B. rpc statements
- C. JSON schema
- D. container statements
- E. XML schema
Answer: CE
NEW QUESTION 8
What is a characteristics of traffic shaping?
- A. can be applied in both traffic direction
- B. queues out-of-profile packets until the buffer is full
- C. drops out-of-profile packets
- D. causes TCP retransmits when packet are dropped
Answer: B
NEW QUESTION 9
DRAG DROP
Drag and drop the characteristics from the left onto the routing protocols they describe on the right.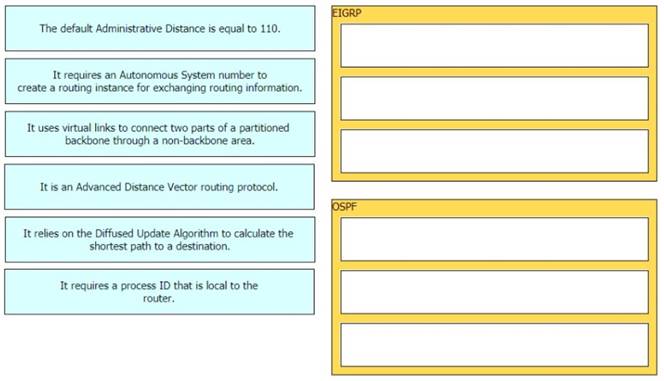
Solution:
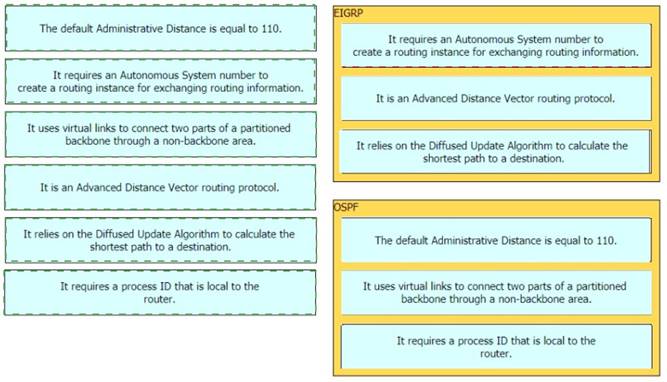
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
Which component of the Cisco Cyber Threat Defense solution provides user and flow context analysis?
- A. Cisco Firepower and FireSIGHT
- B. Cisco Stealth watch system
- C. Advanced Malware Protection
- D. Cisco Web Security Appliance
Answer: B
NEW QUESTION 11
Which TLV value must be added to Option 43 when DHCP is used to ensure that APs join the WLC?
- A. 0x77
- B. AAA
- C. 0xf1
- D. 642
Answer: C
NEW QUESTION 12
What is the difference between CEF and process switching?
- A. CEF processes packets that are too complex for process switching to manage.
- B. CEF is more CPU-intensive than process switching.
- C. CEF uses the FIB and the adjacency table to make forwarding decisions, whereas process switching punts each packet.
- D. Process switching is faster than CEF.
Answer: C
NEW QUESTION 13
A customer has a wireless network deployed within a multi-tenant building. The network provides client access, location-based services, and is monitored using Cisco DNA Center. The security department wants to locate and track malicious devices based on threat signatures. Which feature is required for this solution?
- A. Cisco aWIPS policies on the WLC
- B. Cisco aWIPS policies on Cisco DNA Center
- C. malicious rogue rules on the WLC
- D. malicious rogue rules on Cisco DNA Center
Answer: B
NEW QUESTION 14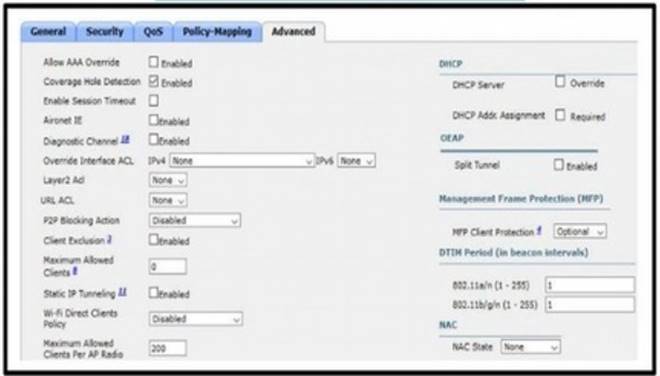
Refer to the exhibit. An engineer has configured Cisco ISE to assign VLANs to clients based on their method of authentication, but this is not working as expected. Which action will resolve this issue?
- A. require a DHCP address assignment
- B. utilize RADIUS profiling
- C. set a NAC state
- D. enable AAA override
Answer: B
NEW QUESTION 15
Refer to the exhibit.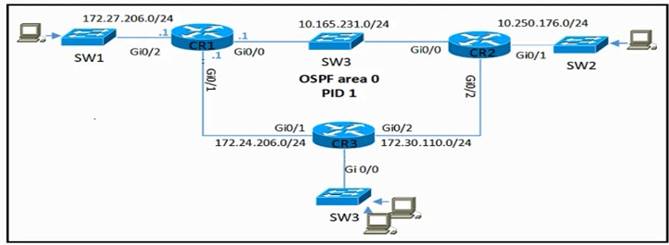
CR2 and CR3 ate configured with OSPF. Which configuration, when applied to CR1. allows CR1 to exchange OSPF Information with CR2 and CR3 but not with other network devices or on new Interfaces that are added to CR1?
A)
B)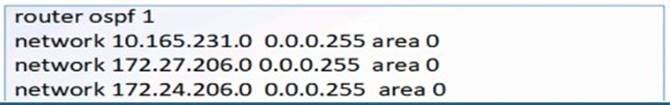
C)
D)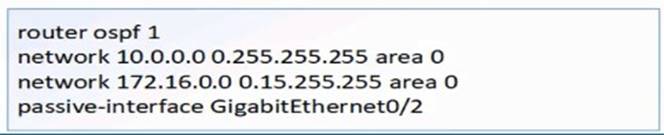
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 16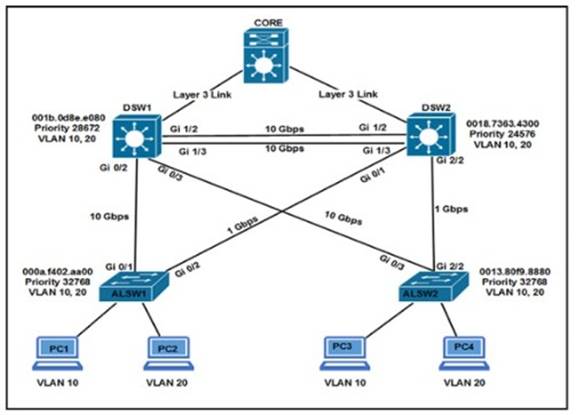
Refer to the exhibit. Which two commands ensure that DSW1 becomes root bridge for VLAN 10? (Choose two)
- A. DSW1(config)#spanning-tree vlan 10 priority 4096 Most Voted
- B. DSW1(config)#spanning-tree vlan 10 priority root
- C. DSW2(config)#spanning-tree vlan 10 priority 61440 Most Voted
- D. DSW1(config)#spanning-tree vlan 10 port-priority 0
- E. DSW2(config)#spanning-tree vlan 20 priority 0
Answer: CD
Explanation:
Ref: Scaling Networks v6 Companion Guide
“STP
…
Extended System ID
…
Bridge Priority
The bridge priority is a customizable value that can be used to influence which switch becomes the root bridge. The switch with the lowest priority, which implies the lowest BID, becomes the root bridge because a lower priority value takes precedence.
…
The default priority value for all Cisco switches is the decimal value 32768. The range is 0 to 61440, in increments of 4096. Therefore, valid priority values are 0, 4096, 8192, 12288, 16384, 20480, 24576, 28672, 32768, 36864, 40960, 45056, 49152, 53248, 57344, and 61440. A bridge priority of 0 takes precedence over all other bridge priorities. All other values are rejected.
NEW QUESTION 17
Which JSON syntax is valid?
A)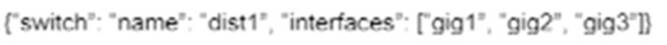
B)
C)
D)
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: C
Explanation:
This JSON can be written as follows:
{
'switch': { 'name': 'dist1',
'interfaces': ['gig1', 'gig2', 'gig3']
}
}
NEW QUESTION 18
An engineer must protect their company against ransom ware attacks. Which solution allows the engineer to block the execution stage and prevent file encryption?
- A. Use Cisco AMP deployment with the Malicious Activity Protection engineer enabled.
- B. Use Cisco AMP deployment with the Exploit Prevention engine enabled.
- C. Use Cisco Firepower and block traffic to TOR networks.
- D. Use Cisco Firepower with Intrusion Policy and snort rules blocking SMB exploitation.
Answer: B
Explanation:
Ransomware are malicious software that locks up critical resources of the users. Ransomware uses well-established public/private key cryptography which leaves the only way of recovering the files being the payment of the ransom, or restoring files from backups.
Cisco Advanced Malware Protection (AMP) for Endpoints Malicious Activity Protection (MAP) engine defends your endpoints by monitoring the system and identifying processes that exhibit malicious activities when they execute and stops them from running. Because the MAP engine detects threats by observing the behavior of the process at run time, it can generically determine if a system is under attack by a new variant of ransomware or malware that may have eluded other security products and detection technology, such as legacy signature-based malware detection. The first release of the MAP engine targets identification, blocking, and quarantine of ransomware attacks on the endpoint.
Reference: https://www.cisco.com/c/dam/en/us/products/collateral/security/ampfor-endpoints/white-paper-c11-740980.pdf
NEW QUESTION 19
What is a client who is running 802.1x for authentication reffered to as?
- A. supplicant
- B. NAC device
- C. authenticator
- D. policy enforcement point
Answer: A
NEW QUESTION 20
Why would a small or mid-size business choose a cloud solution over an on-premises solution?
- A. Cloud provides higher data security than on-premises.
- B. Cloud provides more control over the implementation process than on-premises.
- C. Cloud provides greater ability for customization than on-premises.
- D. Cloud provides lower upfront cost than on-premises.
Answer: C
NEW QUESTION 21
......
Recommend!! Get the Full 350-401 dumps in VCE and PDF From Allfreedumps.com, Welcome to Download: https://www.allfreedumps.com/350-401-dumps.html (New 188 Q&As Version)