Your success in CompTIA N10-008 is our sole target and we develop all our N10-008 braindumps in a way that facilitates the attainment of this target. Not only is our N10-008 study material the best you can find, it is also the most detailed and the most updated. N10-008 Practice Exams for CompTIA N10-008 are written to the highest standards of technical accuracy.
Online CompTIA N10-008 free dumps demo Below:
NEW QUESTION 1
A network technician is configuring a wireless access point and wants to only allow company-owned devices to associate with the network. The access point uses PSKs,
and a network authentication system does not exist on the network. Which of the following should the technician implement?
- A. Captive portal
- B. Guest network isolation
- C. MAC filtering
- D. Geofencing
Answer: C
Explanation:
MAC filtering is a method of allowing only company-owned devices to associate with the network by using their MAC addresses as identifiers. A MAC address is a unique identifier assigned to each network interface card (NIC) by the manufacturer. MAC filtering can be configured on the wireless access point to allow or deny access based on the MAC address of the device. This way, only devices with known MAC addresses can connect to the network. References: https://www.comptia.org/training/books/network-n10-008-study-guide (page 323)
NEW QUESTION 2
A network engineer is investigating reports of poor network performance. Upon reviewing a device configuration, the engineer finds that duplex settings are mismatched on both ends. Which of the following would be the MOST likely result of this finding?
- A. Increased CRC errors
- B. Increased giants and runts
- C. Increased switching loops
- D. Increased device temperature
Answer: A
Explanation:
Mismatched duplex settings can cause an increase in CRC errors, which are errors in data transmission that can result in corrupted data. References: CompTIA Network+ Certification Study Guide, Chapter 4: Infrastructure.
NEW QUESTION 3
Which of the following is the primary function of the core layer of the three-tiered model?
- A. Routing
- B. Repeating
- C. Bridging
- D. Switching
Answer: A
Explanation:
https://www.omnisecu.com/cisco-certified-network-associate-ccna/three-tier-hierarchical-network-model.php
Core Layer consists of biggest, fastest, and most expensive routers with the highest model numbers and Core Layer is considered as the back bone of networks. Core Layer routers are used to merge geographically separated networks. The Core Layer routers move information on the network as fast as possible. The switches operating at core layer switches packets as fast as possible.
NEW QUESTION 4
A technician is investigating why a PC cannot reach a file server with the IP address 192.168.8.129. Given the following TCP/IP network configuration: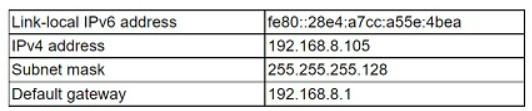
Which of the following configurations on the PC is incorrect?
- A. Subnet mask
- B. IPv4 address
- C. Default gateway
- D. IPv6 address
Answer: C
Explanation:
The default gateway is the IP address of the router that connects the PC to other networks. The default gateway should be on the same subnet as the PC’s IPv4 address. However, in this case, the default gateway is 192.168.9.1, which is on a different subnet than the PC’s IPv4 address of 192.168.8.15. Therefore, the default gateway configuration on the PC is incorrect and prevents the PC from reaching the file server on another subnet.
NEW QUESTION 5
In which of the following components do routing protocols belong in a software-defined network?
- A. Infrastructure layer
- B. Control layer
- C. Application layer
- D. Management plane
Answer: B
Explanation:
A software-defined network (SDN) is a network architecture that decouples the control plane from the data plane and centralizes the network intelligence in a software controller. The control plane is the part of the network that makes decisions about how to route traffic, while the data plane is the part of the network that forwards traffic based on the control plane’s instructions. The control layer is the layer in an SDN that contains the controller and the routing protocols that communicate with the network devices. The control layer is responsible for managing and configuring the network devices and providing them with the necessary information to forward traffic. References: https://www.comptia.org/training/books/network-n10-008-study-guide (page 378)
NEW QUESTION 6
A network administrator is configuring logging on an edge switch. The requirements are to log each time a switch port goes up or down. Which of the following logging levels will provide this information?
- A. Warnings
- B. Notifications
- C. Alert
- D. Errors
Answer: B
Explanation:
Notifications are the lowest logging level and will provide the desired information regarding switch port up/down activity. According to the CompTIA Network+ Study Manual, notifications "are used for logging normal activities, such as port up/down events, link changes, and link flaps."
NEW QUESTION 7
A technician is monitoring a network interface and notices the device is dropping packets. The cable and interfaces, however, are in working order. Which of the following is MOST likely the cause?
- A. OID duplication
- B. MIB mismatch
- C. CPU usage
- D. Encapsulation errors
Answer: C
NEW QUESTION 8
A false camera is installed outside a building to assist with physical security. Which of the following is the device assisting?
- A. Detection
- B. Recovery
- C. Identification
- D. Prevention
Answer: A
NEW QUESTION 9
A network administrator requires redundant routers on the network, but only one default gateway is configurable on a workstation. Which of the following will allow for redundant routers with a single IP address?
- A. EIGRP
- B. VRRP
- C. MPLS
- D. STP
Answer: B
Explanation:
Virtual Router Redundancy Protocol (VRRP) is a protocol that allows for redundant routers on the network with a single IP address. VRRP works by creating a virtual router that consists of one master router and one or more backup routers. The virtual router has its own IP address and MAC address that are shared among the routers in the group. The master router responds to traffic sent to the virtual router’s IP address, while the backup routers monitor the master router’s status. If the master router fails, one of the backup routers takes over as the new master router and continues to respond to traffic. This way, VRRP provides high availability and fault tolerance for the network. References: https://www.comptia.org/training/books/network-n10-008-study-guide (page 230)
NEW QUESTION 10
A customer reports there is no access to resources following the replacement of switches. A technician goes to the site to examine the configuration and discovers redundant links between two switches. Which of the following is the reason the network is not functional?
- A. The ARP cache has become corrupt.
- B. CSMA/CD protocols have failed.
- C. STP is not configured.
- D. The switches are incompatible models
Answer: C
Explanation:
The reason the network is not functional is that STP (Spanning Tree Protocol) is not configured on the switches. STP is a protocol that prevents loops in a network topology by blocking redundant links between switches. If STP is not enabled, the switches will forward broadcast frames endlessly, creating a broadcast storm that consumes network resources and disrupts communication. References: CompTIA Network+ N10-008 Certification Study Guide, page 67; The Official CompTIA Network+ Student Guide (Exam N10-008), page 2-14.
NEW QUESTION 11
An ISP is unable to provide services to a user in a remote area through cable and DSL. Which of the following is the NEXT best solution to provide services without adding external infrastructure?
- A. Fiber
- B. Leased line
- C. Satellite
- D. Metro optical
Answer: C
Explanation:
If an ISP is unable to provide services to a user in a remote area through cable and DSL, the next best solution to provide services without adding external infrastructure would likely be satellite. Satellite is a wireless communication technology that uses a network of satellites orbiting the Earth to transmit and receive data. It is well-suited for providing connectivity to remote or rural areas where other types of infrastructure may not be available or may be cost-prohibitive to install.
NEW QUESTION 12
After rebooting an AP a user is no longer able to conned to me enterprise LAN A technician plugs a laptop In to the same network jack and receives the IP 169.254 0 200. Which of the following is MOST likely causing the issue?
- A. DHCP scope exhaustion
- B. Signal attenuation
- C. Channel overlap
- D. Improper DNS configuration
Answer: A
Explanation:
DHCP scope exhaustion occurs when the number of available IP addresses to be leased from a DHCP server have been used up. This could be caused by a large number of clients on the network, or a misconfigured DHCP scope. When this happens, clients will be assigned an IP address from the APIPA range (169.254.0.0 to 169.254.255.255). To resolve this issue, the DHCP scope needs to be expanded or adjusted to accommodate the number of clients on the network.
NEW QUESTION 13
Which of the following issues are present with RIPv2? (Select TWO).
- A. Route poisoning
- B. Time to converge
- C. Scalability
- D. Unicast
- E. Adjacent neighbors
- F. Maximum transmission unit
Answer: BC
Explanation:
The disadvantages of RIP (Routing Information Protocol) include the following.
---Outdated, insecure, and slow. This is your parents' protocol. It was a thing before the Web was born.
---The more well-known problem of the 15 hop limitation in which data must travel
---Convergence time is terrible for information propagation in a network
---Metrics. It determines the number of hops from source to destination, and gives no regard to other factors when determining the best path for data to travel
---Overhead. A good example would be routing tables. These are broadcast at half-minute intervals to other routers regardless of whether the data has changed or not. It's essentially like those old cartoons where the town guard in the walled city cries out, '10 o' the clock and all is well!'.
RIPv2 introduced more security and reduced broadcast traffic, which is relevant for some available answers here.
NEW QUESTION 14
A divide-and-conquer approach is a troubleshooting method that involves breaking a complex problem into smaller and more manageable parts, and then testing each part to isolate the cause of the problem. In this scenario, the technician is using a divide-and- conquer approach by pinging the default gateway and DNS server of the workstation, which are two possible sources of connectivity issues. By pinging these devices, the technician can determine if the problem is related to the local network or the external network.
Which of the following most likely requires the use of subinterfaces?
- A. A router with only one available LAN port
- B. A firewall performing deep packet inspection
- C. A hub utilizing jumbo frames
- D. A switch using Spanning Tree Protocol
Answer: A
Explanation:
Subinterfaces are logical divisions of a physical interface that allow a router to communicate with multiple networks using a single LAN port. Subinterfaces can have different IP addresses, VLANs, and routing protocols. They are useful for reducing the number of physical interfaces and cables needed, as well as improving network performance and security.
References:
✑ Subinterfaces - CompTIA Network+ N10-008 Domain 1.21 - YouTube1
✑ CompTIA Network+ Certification Exam Objectives, page 92
NEW QUESTION 15
During a client audit, a network analyst is tasked with recommending changes to upgrade the client network and readiness. Afield technician has submitted the following report: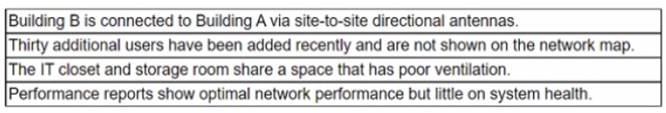
Based on this report, which of the following metrics or sensors would be the BEST recommendation to the client?
- A. Electrical
- B. Humidity
- C. Flooding
- D. Temperature
Answer: B
Explanation:
Humidity is the amount of water vapor in the air. High humidity can cause corrosion, condensation, and short circuits in electronic devices. Low humidity can cause static electricity and damage sensitive components. The optimal humidity range for a data center is between 40% and 60%. Based on the report, the humidity level in the server room is 70%, which is too high and can affect the performance and reliability of the network equipment. Therefore, the best recommendation to the client is to install a humidity sensor and a dehumidifier to control the humidity level in the server room.
References: Network+ Study Guide Objective 5.1: Summarize the importance of physical security controls.
NEW QUESTION 16
A user reports that a new VoIP phone works properly but the computer that is connected to the phone cannot access any network resources. Which of the following MOST Likely needs to be configured correctly to provide network connectivity to the computer?
- A. Port duplex settings
- B. Port aggregation
- C. ARP settings
- D. VLAN tags
- E. MDIX settings
Answer: D
Explanation:
VLAN (virtual LAN) tags are used to identify packets as belonging to a particular VLAN. VLANs are used to segment a network into logical sub-networks, and each VLAN is assigned a unique VLAN tag. If the VLAN tag is not configured correctly, the computer may not be able to access network resources.
NEW QUESTION 17
A systems administrator needs to improve WiFi performance in a densely populated office tower and use the latest standard. There is a mix of devices that use 2.4 GHz and 5 GHz. Which of the following should the systems administrator select to meet this requirement?
- A. 802.11ac
- B. 802.11ax
- C. 802.11g
- D. 802.11n
Answer: B
Explanation:
802.11ax is the latest WiFi standard that improves WiFi performance in densely populated environments and supports both 2.4 GHz and 5 GHz bands. 802.11ac is the previous standard that only supports 5 GHz band. 802.11g and 802.11n are older standards that support 2.4 GHz band only or both bands respectively. References: https://partners.comptia.org/docs/default-source/resources/comptia-network-n10-008-exam-objectives-(2-0), https://www.techtarget.com/searchnetworking/tip/Whats-the-difference-between-80211ax-vs-80211ac
NEW QUESTION 18
......
Thanks for reading the newest N10-008 exam dumps! We recommend you to try the PREMIUM Dumps-files.com N10-008 dumps in VCE and PDF here: https://www.dumps-files.com/files/N10-008/ (877 Q&As Dumps)