Cause all that matters here is passing the CompTIA N10-008 exam. Cause all that you need is a high score of N10-008 CompTIA Network+Exam exam. The only one thing you need to do is downloading Testking N10-008 exam study guides now. We will not let you down with our money-back guarantee.
Free demo questions for CompTIA N10-008 Exam Dumps Below:
NEW QUESTION 1
Which of the following would be the BEST choice to connect branch sites to a main office securely?
- A. VPN headend
- B. Proxy server
- C. Bridge
- D. Load balancer
Answer: A
Explanation:
Host-to-Site, or Client-to-Site, VPN allows for remote servers, clients, and other hosts to establish tunnels through a VPN gateway (or VPN headend) via a private network. The tunnel between the headend and the client host encapsulates and encrypts data.
NEW QUESTION 2
A corporation is looking for a method to secure all traffic between a branch office and its data center in order to provide a zero-touch experience for all staff members who work there. Which of the following would BEST meet this requirement?
- A. Site-to-site VPN
- B. VNC
- C. Remote desktop gateway
- D. Virtual LANs
Answer: A
Explanation:
A site-to-site VPN is a method that creates a secure and encrypted connection between two internet gateways, such as routers or firewalls, that belong to different networks1. A site-to-site VPN can secure all traffic between a branch office and its data center by creating a virtual tunnel that protects the data from interception or tampering. A site-to-site VPN can also provide a zero-touch experience for all staff members who work there, as they do not need to install any software or configure any settings on their devices to access the data center resources. They can simply use their local network as if they were physically connected to the data center network.
VNC (Virtual Network Computing) is a method that allows remote access and control of a computer’s desktop from another device over a network2. VNC can enable staff members to work remotely by accessing their office computers from their home computers or mobile devices. However, VNC does not secure all traffic between a branch office and its data center, as it only works at the application layer and does not encrypt the network layer. VNC also does not provide a zero-touch experience for staff members, as they need to install software and configure settings on both the host and the client devices.
Remote desktop gateway is a method that allows remote access and control of a
computer’s desktop from another device over a network using the Remote Desktop Protocol (RDP). Remote desktop gateway can also enable staff members to work remotely by accessing their office computers from their home computers or mobile devices. However, remote desktop gateway does not secure all traffic between a branch office and its data center, as it only works at the application layer and does not encrypt the network layer. Remote desktop gateway also does not provide a zero-touch experience for staff members, as they need to install software and configure settings on both the host and the client devices.
Virtual LANs (VLANs) are methods that create logical subdivisions of a physical network based on criteria such as function, department, or security level. VLANs can improve network performance, security, and management by reducing broadcast domains, isolating traffic, and enforcing policies. However, VLANs do not secure all traffic between a branch office and its data center, as they only work at the data link layer and do not encrypt the network layer. VLANs also do not provide a zero-touch experience for staff members, as they need to configure settings on their network devices to join or leave a VLAN.
NEW QUESTION 3
Which of the following will reduce routing table lookups by performing packet forwarding decisions independently of the network layer header?
- A. MPLS
- B. mGRE
- C. EIGRP
- D. VRRP
Answer: A
Explanation:
Multiprotocol Label Switching, or MPLS, is a networking technology that routes traffic using the shortest path based on “labels,” rather than network addresses, to handle forwarding over private wide area networks. As a scalable and protocol- independent solution, MPLS assigns labels to each data packet, controlling the path the packet follows. MPLS greatly improves the speed of traffic, so users don’t experience downtime when connected to the network.
NEW QUESTION 4
A network security engineer is responding to a security incident. The engineer suspects that an attacker used an authorized administrator account to make configuration changes to the boundary firewall. Which of the following should the network security engineer review?
- A. Network traffic logs
- B. Audit logs
- C. Syslogs
- D. Event logs
Answer: B
Explanation:
Audit logs are records of the actions performed by users or processes on a system or network device. They can provide information about who made what changes, when, and why. Audit logs are essential for detecting and investigating security incidents, as well as for ensuring compliance with policies and regulations. Audit logs can help the network security engineer to identify the source of the unauthorized configuration changes to the boundary firewall, as well as the scope and impact of the changes.
References1 - Changes to Cyber Essentials requirements – April 2021 update2 - 8 Firewall Best Practices for Securing the Network3 - How to secure your network boundaries with a firewall
NEW QUESTION 5
Given the following Information: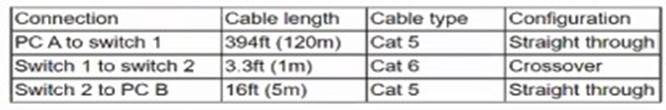
Which of the following would cause performance degradation between PC A and PC B'?
- A. Attenuation
- B. Interference
- C. Decibel loss
- D. Incorrect pinout
Answer: D
NEW QUESTION 6
Which of the following would need to be configured to ensure a device with a specific MAC address is always assigned the same IP address from DHCP?
- A. Scope options
- B. Reservation
- C. Dynamic assignment
- D. Exclusion
- E. Static assignment
Answer: B
Explanation:
A reservation should be configured to ensure a device with a specific MAC address is always assigned the same IP address from DHCP. A reservation is a feature of DHCP that allows an administrator to assign a fixed IP address to a device based on its MAC address. This way, the device will always receive the same IP address from the DHCP server, even if it is powered off or disconnected from the network for a long time. References: https://docs.microsoft.com/en-us/windows-server/troubleshoot/configure-dhcp- reservations
NEW QUESTION 7
Which of the following connectors and terminations are required to make a Cat 6 cable that connects from a PC to a non-capable MDIX switch? (Select TWO).
- A. T1A-568-A - TIA-568-B
- B. TIA-568-B - TIA-568-B
- C. RJ11
- D. RJ45
- E. F-type
Answer: AD
NEW QUESTION 8
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution. Which of the following
records should be used to accomplish the task?
- A. TXT
- B. AAA
- C. PTR
- D. CNAME
Answer: D
Explanation:
CNAME stands for Canonical Name, and it is a type of DNS record that creates an alias for another domain name. A CNAME record can be used to redirect a network resource that has been moved to a different location, such as a SaaS solution. For example, if a web server that was previously hosted on the local network with the domain name www.example.com is now hosted by a SaaS provider with the domain name www.saasprovider.com, a CNAME record can be created to point www.example.com to www.saasprovider.com. This way, the users can still access the web server using the original domain name, and the DNS server will resolve it to the new domain name. References
✑ CNAME is one of the common DNS record types covered in Objective 1.6 of the
CompTIA Network+ N10-008 certification exam1.
✑ CNAME can be used to redirect a network resource that has been moved to a different location23.
✑ CNAME creates an alias for another domain name23.
1: CompTIA Network+ Certification Exam Objectives, page 4 2: DNS Record Types – N10- 008 CompTIA Network+ : 1.6 3: The Official CompTIA Network+ Student Guide (Exam N10-008), Chapter 1, page 32
NEW QUESTION 9
A network technician is investigating a trouble ticket for a user who does not have network connectivity. All patch cables between the wall jacks and computers in the building were upgraded over the weekend from Cat 5 to Cat 6. The newly installed cable is crimped With a TIA/EIA 568A on one end and a TIA/EIA 568B on the other end. Which of the following should the technician do to most likely fix the issue?
- A. Ensure the switchport has POE enabled.
- B. Crimp the cable as a straight-through cable.
- C. Ensure the switchport has STP enabled.
- D. Crimp the cable as a rollover cable.
Answer: B
Explanation:
Crimping the cable as a straight-through cable is the most likely fix for the issue where users are unable to access any network resources after upgrading from Cat 5 to Cat 6 cables. Crimping is a process of attaching connectors to the ends of cables using a tool called a crimper. A straight-through cable is a type of twisted-pair cable that has the same wiring scheme on both ends, meaning that each pin on one end is connected to the same pin on the other end. A straight-through cable is used to connect devices that operate on different layers of the OSI model, such as a computer and a switch, or a switch and a router. If the newly installed cable is crimped with TIA/EIA 568A on one end and TIA/EIA 568B on the other end, it becomes a crossover cable. A crossover cable is a type of twisted-pair cable that has opposite wiring schemes on both ends, meaning that each pin on one end is connected to a different pin on the other end. A crossover cable is used to connect devices that operate on the same layer of the OSI model, such as two computers or two switches. Using a crossover cable instead of a straight-through cable can cause network communication errors or failures. References: [CompTIA Network+ Certification Exam Objectives], Straight Through vs Crossover Cable: What’s The Difference?
NEW QUESTION 10
A network administrator is configuring a load balancer for two systems. Which of the following must the administrator configure to ensure connectivity during a failover?
- A. VIP
- B. NAT
- C. APIPA
- D. IPv6 tunneling
- E. Broadcast IP
Answer: A
Explanation:
A virtual IP (VIP) address must be configured to ensure connectivity during a failover. A VIP address is a single IP address that is assigned to a group of servers or network devices. When one device fails, traffic is automatically rerouted to the remaining devices, and the VIP address is reassigned to the backup device, allowing clients to continue to access the service without interruption.
References:
✑ CompTIA Network+ Certification Study Guide, Exam N10-007, Fourth Edition, Chapter 6: Network Servers, p. 300
NEW QUESTION 11
Which of the following policies is MOST commonly used for guest captive portals?
- A. AUP
- B. DLP
- C. BYOD
- D. NDA
Answer: A
Explanation:
AUP stands for Acceptable Use Policy, which is a policy that defines the rules and guidelines for using a network or service. A guest captive portal is a web page that requires users to agree to the AUP before accessing the Internet or other network resources. This is a common way to enforce security and legal compliance for guest users. References: https://www.arubanetworks.com/techdocs/Instant_87_WebHelp/Content/instant-ug/captive- portal/captive-portal.htm
NEW QUESTION 12
An attacker is attempting to find the password to a network by inputting common words and phrases in plaintext to the password prompt. Which of the following attack types BEST describes this action?
- A. Pass-the-hash attack
- B. Rainbow table attack
- C. Brute-force attack
- D. Dictionary attack
Answer: D
Explanation:
The attacker attempting to find the password to a network by inputting common words and phrases in plaintext to the password prompt is using a dictionary attack. References: CompTIA Network+ Certification Study Guide, Chapter 6: Network Attacks and Mitigation.
NEW QUESTION 13
A technician is consolidating a topology with multiple SSlDs into one unique SSiD deployment. Which of the following features will be possible after this new configuration?
- A. Seamless roaming
- B. Basic service set
- C. WPA
- D. MU-MIMO
Answer: A
NEW QUESTION 14
A company realizes that only half of its employees work in the office, and the employees who work from home no longer need a computer at the office. Which of the following security measures should the network administrator implement when removing a computer from a cubicle?
- A. Disable DHCP on the computer being removed.
- B. Place the switch port in a private VLAN.
- C. Apply a firewall rule to block the computer's IP address.
- D. Remove the employee's network access.
Answer: D
Explanation:
The best security measure to implement when removing a computer from a cubicle is to remove the employee’s network access. This will prevent the employee from accessing any network resources or data from the computer, as well as prevent any unauthorized users from using the computer to access the network. Removing the employee’s network access can be done by deleting or disabling the user account, revoking the credentials, or changing the permissions.
The other options are not as effective or necessary as removing the employee’s network access. They are:
•Disabling DHCP on the computer being removed will prevent the computer from obtaining an IP address from the network, but it will not prevent the computer from using a static IP address or accessing the network through another device.
•Placing the switch port in a private VLAN will isolate the computer from other devices on the network, but it will not prevent the computer from accessing the network through another port or device.
•Applying a firewall rule to block the computer’s IP address will prevent the computer from communicating with the network, but it will not prevent the computer from changing its IP address or accessing the network through another device.
References
1: CompTIA Network+ N10-008 Cert Guide - O’Reilly Media 2: Network+ (Plus) Certification | CompTIA IT Certifications
3: 10 Ways to Secure Office Workstations - Computer Security
NEW QUESTION 15
A city has hired a new employee who needs to be able to work when traveling at home and at the municipal sourcing of a neighboring city that snares services. The employee is issued a laptop, and a technician needs to train the employee on the appropriate solutions
for secure access to the network from all the possible locations On which of the following solutions would the technician MOST likely train the employee?
- A. Site-to-site VPNs between the two city locations and client-to-site software on the employee's laptop tor all other remote access
- B. Client-to-site VPNs between the travel locations and site-to-site software on the employee's laptop for all other remote access
- C. Client-to-site VPNs between the two city locations and site-to-site software on the employee's laptop for all other remote access
- D. Site-to-site VPNs between the home and city locations and site-to-site software on the employee's laptop for all other remote access
Answer: A
Explanation:
The technician would most likely train the employee on using site-to-site VPNs between the two city locations and client-to-site software on the employee’s laptop for all other remote access. A VPN (Virtual Private Network) is a technology that creates a secure and encrypted tunnel over a public network such as the Internet. It allows remote users or sites to access a private network as if they were directly connected to it. A site-to- site VPN connects two or more networks, such as branch offices or data centers, using a VPN gateway device at each site. A client-to-site VPN connects individual users, such as mobile workers or telecommuters, using a VPN client software on their devices. In this scenario, the employee needs to access the network from different locations, such as home, travel, or another city. Therefore, the technician would train the employee on how to use site-to-site VPNs to connect to the network from another city location that shares services, and how to use client-to-site software to connect to the network from home or travel locations. References: https://www.cisco.com/c/en/us/support/docs/security- vpn/ipsec-negotiation-ike-protocols/14106-how-vpn-works.html
NEW QUESTION 16
A network administrator redesigned the positioning of the APs to create adjacent areas of wireless coverage. After project validation, some users still report poor connectivity when their devices maintain an association to a distanced AP. Which of the following should the network administrator check FIRST?
- A. Validate the roaming settings on the APs and WLAN clients
- B. Verify that the AP antenna type is correct for the new layout
- C. Check to see if MU-MIMO was properly activated on the APs
- D. Deactivate the 2.4GHz band on the APS
Answer: A
Explanation:
The network administrator should check the roaming settings on the APs and WLAN clients first. Roaming is the process of switching from one AP to another without losing connectivity. If the roaming settings are not configured properly, some users may experience poor connectivity when their devices stay connected to a distant AP instead of switching to a closer one. References: https://www.cisco.com/c/en/us/support/docs/wireless-mobility/wireless-lan-wlan/82068- roam-faq.html
NEW QUESTION 17
A network technician is reviewing an upcoming project's requirements to implement laaS. Which of the following should the technician consider?
- A. Software installation processes
- B. Type of database to be installed
- C. Operating system maintenance
- D. Server hardware requirements
Answer: D
Explanation:
IaaS stands for Infrastructure as a Service, which is a cloud computing model that provides virtualized computing resources such as servers, storage, and networking over the Internet. When implementing IaaS, the network technician should consider the server hardware requirements, such as CPU, RAM, disk space, and network bandwidth, that are needed to run the applications and services on the cloud. The other options are not relevant to IaaS, as they are either handled by the cloud provider or by the end-user. References: https://www.comptia.org/blog/what-is-iaas
NEW QUESTION 18
......
100% Valid and Newest Version N10-008 Questions & Answers shared by Dumpscollection.com, Get Full Dumps HERE: https://www.dumpscollection.net/dumps/N10-008/ (New 877 Q&As)