we provide Refined CompTIA SK0-005 test preparation which are the best for clearing SK0-005 test, and to get certified by CompTIA CompTIA Server+ Certification Exam. The SK0-005 Questions & Answers covers all the knowledge points of the real SK0-005 exam. Crack your CompTIA SK0-005 Exam with latest dumps, guaranteed!
Also have SK0-005 free dumps questions for you:
NEW QUESTION 1
A backup application is copying only changed files each time it runs. During a restore, however, only a single file is used. Which of the following backup methods does this describe?
- A. Open file
- B. Synthetic full
- C. Full incremental
- D. Full differential
Answer: B
Explanation:
This is the best description of a synthetic full backup method because it creates a full backup by combining previous incremental backups with the latest backup. An incremental backup copies only the files that have changed since the last backup, while a full backup copies all the files. A synthetic full backup reduces the storage space and network bandwidth required for backups, while also simplifying the restore process by using a single file.References:https://www.veritas.com/support/en_US/doc/129705091- 129705095-0/br731_wxrt-tot_v131910378-129705095
NEW QUESTION 2
An administrator needs to increase the size of an existing RAID 6 array that is running out of available space. Which of the following is the best way the administrator can perform this task?
- A. Replace all the array drives at once and then expand the array.
- B. Expand the array by changing the RAID level to 6.
- C. Expand the array by changing the RAID level to 10.
- D. Replace the array drives one at a time and then expand the array.
Answer: D
Explanation:
RAID 6 is a type of RAID that uses block-level striping with two parity blocks distributed across all member disks. It allows for two disk failures within the RAID set before any data is lost1. A minimum of four disks is requiredto create RAID 61. To increase the size of an existing RAID 6 array, the administrator can replace the array drives one at a time with larger drives and then expand the array. This way, the data and parity are rebuilt on each new drive and the array remains operational during the process2.
NEW QUESTION 3
Which of the following is the most effective way to mitigate risks associated with privacy- related data leaks when sharing with a third party?
- A. Third-party acceptable use policy
- B. Customer data encryption and masking
- C. Non-disclosure and indemnity agreements
- D. Service- and operational-level agreements
Answer: B
Explanation:
The most effective way to mitigate risks associated with privacy-related data leaks when sharing with a third party is customer data encryption and masking. Encryption is a process of transforming data into an unreadable format that can only be decrypted with a key or password. Masking is a process of hiding or replacing sensitive data with fake or meaningless data. By encrypting and masking customer data, the organization can protect the confidentiality and integrity of the data and prevent unauthorized access or disclosure by the third party.
References: CompTIA Server+ SK0-005 Certification Study Guide, Chapter 3, Lesson 3.3, Objective 3.3
NEW QUESTION 4
A backup application is copying only changed files each line it runs. During a restore, however, only a single file is used. Which of the following backup methods does this describe?
- A. Open file
- B. Synthetic full
- C. Full Incremental
- D. Full differential
Answer: B
Explanation:
A synthetic full backup is a backup method that describes copying only changed files each time it runs and using only a single file during a restore. A synthetic full backup is a backup approach that involves creating a new full backup by using the previous full backup and related incremental backups. This means that a backup solution does not have to transfer the full amount of data from the source machine and can synthetize the latest incremental backups with the last full backup to create a new full backup. This reduces the backup window and network bandwidth consumption. During a restore, only the latest synthetic full backup file is needed to recover the data. Open file backup is a backup method that allows backing up files that are in use or locked by applications. Full incremental backup is a backup method that involves performing a full backup first and then backing up only the changed files since the last backup. Full differential backup is a backup method that involves performing a full backup first and then backing up only the changed files since the last full backup. References: https://www.nakivo.com/blog/what-is- synthetic-backup/https://www.howtogeek.com/192115/what-you-need-to-know-about-creating-system-image-backups/
NEW QUESTION 5
A technician needs to set up a server backup method for some systems. The company’s management team wants to have quick restores but minimize the amount of backup media required. Which of the following are the BEST backup methods to use to support the management’s priorities? (Choose two.)
- A. Differential
- B. Synthetic full
- C. Archive
- D. Full
- E. Incremental
- F. Open file
Answer: AE
Explanation:
The best backup methods to use to support the management’s priorities are differential and incremental. A backup is a process of copying data from a source to a destination for the purpose of restoring it in case of data loss or corruption. There are different types of backup methods that vary in terms of speed, efficiency, and storage requirements. Differential and incremental backups are two types of partial backups that only copy the data that has changed since the last full backup. A full backup is a type of backup that copies all the data from the source to the destination. A full backup provides the most complete and reliable restore option, but it also takes the longest time and requires the most storage space. A differential backup copies only the data that has changed since the last full backup. A differential backup provides a faster restore option than an incremental backup, but it also takes more time and requires more storage space than an incremental backup. An incremental backup copies only the data that has changed since the last backup, whether it was a full or an incremental backup. An incremental backup provides the fastest and most efficient backup option, but it also requires multiple backups to restore the data completely.
NEW QUESTION 6
An administrator is installing a new file server that has four drive bays available. Which of the following RAID types would provide the MOST storage as well as disk redundancy?
- A. RAIDO
- B. RAID 1
- C. RAID 5
- D. RAID 10
Answer: C
Explanation:
RAID 5 is a RAID level that provides striping with parity, which means that data is distributed across all disks with one disk storing parity information for error correction. RAID 5 can tolerate one disk failure without losing data. RAID 5 provides the most storage as well as disk redundancy out of the four RAID levels given, since it only uses one disk for parity and the rest for data. For example, if four 200GB drives are used in a RAID 5 array, the total storage capacity would be 600GB (200GB x 3), while in RAID 0 it would be 800GB (200GB x 4), in RAID 1 it would be 200GB (200GB x 1), and in RAID 10 it would be 400GB (200GB x 2).References:https://en.wikipedia.org/wiki/Standard_RAID_levels#RAID_5
NEW QUESTION 7
A server administrator just installed a new physical server and needs to harden the applications on the server. Which of the following best describes a method of application hardening?
- A. Install the latest patches.
- B. Disable unneeded hardware.
- C. Set the boot order.
- D. Enable a BIOS password.
Answer: A
Explanation:
A method of application hardening is installing the latest patches. Application hardening is a process of reducing the attack surface and vulnerabilities of an application by applying security measures and best practices. Installing the latest patches is one way to harden an application, as patches are updates that fix bugs, errors, or security issues in an application. By installing the latest patches, an application can be protected from known exploits or threats.
References: CompTIA Server+ SK0-005 Certification Study Guide, Chapter 3, Lesson 3.5, Objective 3.5
NEW QUESTION 8
A newly installed server is accessible to local users, but remote users are unable to connect. Which of the following is MOST likely misconfigured?
- A. The IP address
- B. The default gateway
- C. The VLAN
- D. The subnet mask
Answer: B
Explanation:
This is the most likely misconfigured setting because the default gateway is the router that connects the local network to other networks. If the default gateway is incorrect, the server will not be able to communicate with remote users or devices outside its own subnet.
References:https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/ipconfig
NEW QUESTION 9
A company’s IDS has identified outbound traffic from one of the web servers coming over port 389 to an outside address. This server only hosts websites. The company’s SOC administrator has asked a technician to harden this server. Which of the following would be the BEST way to complete this request?
- A. Disable port 389 on the server
- B. Move traffic from port 389 to port 443
- C. Move traffic from port 389 to port 637
- D. Enable port 389 for web traffic
Answer: A
Explanation:
The best way to complete the request to harden the server is to disable port 389 on the server. Port 389 is the default port used by LDAP (Lightweight Directory Access Protocol), which is a protocol that allows access and modification of directory services over a network. LDAP can be used for authentication, authorization, or information retrieval purposes. However, LDAP does not encrypt its data by default, which can expose sensitive information or credentials to attackers who can intercept or modify the network traffic.
Therefore, port 389 should be disabled on a web server that only hosts websites and does not need LDAP functionality. Alternatively, port 636 can be used instead of port 389 to enable LDAPS (LDAP over SSL/TLS), which encrypts the data using SSL/TLS certificates.
NEW QUESTION 10
Which of the following backup methods protects all the changes that have occurred since the last full backup?
- A. Incremental
- B. Archive
- C. Differential
- D. Snapshot
Answer: C
Explanation:
A differential backup is a backup method that protects all the changes that have occurred since the last full backup. A differential backup copies all the files that have been added or modified since the last full backup, regardless of whether they have been backed up before or not. A differential backup does not reset the archive bit of the files, which means they will be backed up again in the next differential backup. A differentialbackup requires more storage space and time than an incremental backup, but it simplifies the restoration process, as only the last full backup and the last differential backup are needed to restore the data
NEW QUESTION 11
A server administrator is currently working on an incident. Which of the following steps should the administrator perform before resolving the issue?
- A. Inform the impacted users.
- B. Make the changes to the system.
- C. Determine the probable causes.
- D. Identify changes to the server.
Answer: C
Explanation:
The step that the server administrator should perform before resolving the issue is to determine the probable causes. This step is part of the troubleshooting process that follows a logical and systematic approach to identify and solve problems with servers and applications. The troubleshooting process consists of several steps, such as:
✑ Identify the problem: Gather information from various sources, such as users, logs, or alerts, to understand the symptoms and scope of the problem.
✑ Establish a theory of probable cause: Analyze the information and formulate one or more possible causes of the problem based on evidence or experience.
✑ Test the theory to determine cause: Perform tests or experiments to verify or eliminate each possible cause until the root cause is found.
✑ Establish a plan of action to resolve the problem and implement the solution: Design and execute a plan to fix the problem using appropriate tools and techniques.
✑ Verify full system functionality and implement preventive measures: Confirm that the problem is resolved and that no other issues arise as a result of the solution. Implement preventive measures to avoid recurrence of the problem or improve performance.
✑ Document findings, actions, and outcomes: Record the details of the problem, its cause, its solution, and its outcome for future reference or knowledge
sharing. References: [CompTIA Server+ Certification Exam Objectives], Domain 6.0: Troubleshooting, Objective 6.1: Given a scenario involving server hardware issues (e.g., power supply failure), troubleshoot using appropriate tools.
NEW QUESTION 12
Users have noticed a server is performing below Baseline expectations. While diagnosing me server, an administrator discovers disk drive performance has degraded. The administrator checks the diagnostics on the RAID controller and sees the battery on me controller has gone bad. Which of the following is causing the poor performance on the RAID array?
- A. The controller has disabled the write cache.
- B. The controller cannot use all the available channels.
- C. The drive array is corrupt.
- D. The controller has lost its configuration.
Answer: A
Explanation:
The write cache is a feature of some RAID controllers that allows them to temporarily store data in a fast memory buffer before writing it to the disk drives. This improves the performance and efficiency of write operations, especially for random and small writes. However, if the battery on the controller goes bad, the controller may disable the write cache to prevent data loss in case of a power failure. This can degrade the disk drive performance significantly, as every write operation will have to wait for the disk drives to complete. References: https://www.dell.com/support/kbdoc/en-us/000131486/understanding-raid-controller-battery-learn-cyclehttps://www.techrepublic.com/article/understanding-raid-controller-write-cache/
NEW QUESTION 13
After the installation of an additional network card into a server, the server will not boot into the OS. A technician tests the network card in a different server with a different OS and verifies the card functions correctly. Which of the following should the technician do NEXT to troubleshoot this issue?
- A. Remove the original network card and attempt to boot using only the new network card.
- B. Check that the BIOS is configured to recognize the second network card.
- C. Ensure the server has enough RAM to run a second network card.
- D. Verify the network card is on the HCL for the OS.
Answer: D
Explanation:
The HCL stands for Hardware Compatibility List and it is a list of hardware devices that are tested and certified to work with a specific operating system. If a network card is not on the HCL for the OS, it may not function properly or cause compatibility issues. Therefore, verifying the network card is on the HCL for the OS should be the next step to troubleshoot this issue.References: https://www.comptia.org/training/resources/exam-objectives/comptia-server-sk0-005-exam- objectives (Objective 4.1)
NEW QUESTION 14
A technician is creating a network snare that will be used across both Unix and Windows clients at the same time. Users need read and write access to the files. Which of the following would be BEST for the technician to deploy?
- A. iSCSI
- B. CIFS
- C. HTTPS
- D. DAS
Answer: B
Explanation:
CIFS (Common Internet File System) is a protocol that allows file sharing across different operating systems, such as Unix and Windows. It supports read and write access to files and folders on a network share. It is also known as SMB (Server Message Block). Verified References: [CIFS], [File sharing]
NEW QUESTION 15
A server administrator is completing an OS installation for a new server. The administrator patches the server with the latest vendor-suggested software, configures DHCP, and verifies all network cables are properly connected in the IDF, but there is no network connectivity. Which of the following is the MOST likely reason for the lack of connectivity?
- A. The VLAN Is improperly configured.
- B. The DNS configuration Is invalid.
- C. The OS version is not compatible with the network switch vendor.
- D. The HIDS is preventing the connection.
Answer: A
Explanation:
If the server administrator patches the server with the latest vendor- suggested software, configures DHCP, and verifies all network cables are properly connected in the IDF, but there is no network connectivity, then the most likely reason for the lack of connectivity is that the VLAN is improperly configured. A VLAN (Virtual Local Area Network) is a logical grouping of network devices that share the same broadcast domain and can communicate with each other without routing. If the server is assigned to a different VLAN than the DHCP server or the default gateway, itwill not be able to obtain an IP address or reach other network devices. The DNS configuration is not relevant for network connectivity, as DNS only resolves names to IP addresses. The OS version is not likely to be incompatible with the network switch vendor, as most network switches use standard protocols and interfaces. The HIDS (Host-based Intrusion Detection System) is not likely to prevent the connection, as HIDS only monitors and alerts on suspicious activities on the host. References: https://www.howtogeek.com/190014/virtualization- basics-understanding-techniques-and-fundamentals/ https://www.howtogeek.com/164981/how-to-use-nslookup-to-check-domain-name-information-in-microsoft-windows/https://www.howtogeek.com/202794/what-is-an-intrusion-detection-system-ids-and-how-does-it-work/
NEW QUESTION 16
A server administrator is instating a new server in a data center. The administrator connects the server to a midplane but does not connect any cables Which of the following types of servers is the administrator MOST likely installing?
- A. Rack
- B. Virtual
- C. Tower
- D. Blade
Answer: D
Explanation:
A blade server is a type of server that is installed in a chassis or an enclosure that provides power, cooling, networking, and management features. The blade server does not have any cables attached to it, as it connects to the chassis through a midplane or a backplane. A blade server can save space, energy, and cost compared to other types of servers. Verified References: [Blade server], [Chassis]
NEW QUESTION 17
A technicianretailed a new4TBharddrive inaWindows server. Which of the following should the technician perform FIRST to provision the newdrive?
- A. Configure the drive as a base disk.
- B. Configure the drive as a dynamic disk.
- C. Partition the drive using MBR.
- D. Partition the drive using OPT.
Answer: D
Explanation:
GPT (GUID Partition Table) is a partitioning scheme that allows creating partitions on large hard drives (more than 2 TB). It supports up to 128 partitions per drive and uses 64-bit addresses to locate them. MBR (Master Boot Record) is an older partitioning scheme that has limitations on the size and number of partitions (up to 4 primary partitions or 3 primary and 1 extended partition per drive). To provision a new 4 TB drive, the technician should partition it using GPT. Verified References: [GPT], [MBR]
NEW QUESTION 18
An application server cannot communicate with a newly installed database server. The database server, which has static IP information, is reading the following output from ipconf ig: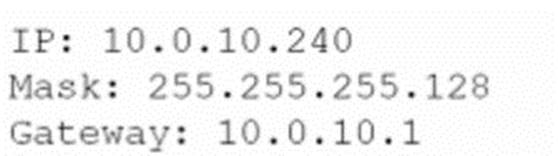
The application server is reading the following output from ipconf ig: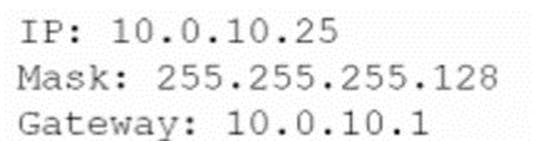
Which of the following most likely contains an error?
- A. IP address
- B. DHCP
- C. Gateway
- D. Subnet mask
Answer: D
Explanation:
The subnet mask is most likely containing an error that prevents the application server from communicating with the newly installed database server. The subnet mask is a binary number that defines how many bits of an IP address are used for the network portion and how many bits are used for the host portion. The subnet mask determines which devices belong to the same network or subnet and can communicate directly with each other without routing or switching devices. The subnet mask of the database server is 255.255.O.O, which means that all 32 bits of its IP address are used for the network portion and none for the host portion, which is invalid and makes it unreachable by any other device on any network or subnet. The subnet mask of the application server is 255.O.O.O, which means that only 8 bits of its IP address are used for the network portion and 24 bits are used for the host portion, which is also uncommon and makes it incompatible with most networks or subnets. References: [CompTIA Server+ Certification Exam Objectives], Domain 4.0: Networking, Objective 4.1: Given a scenario, configure network settings for servers.
NEW QUESTION 19
......
P.S. Allfreedumps.com now are offering 100% pass ensure SK0-005 dumps! All SK0-005 exam questions have been updated with correct answers: https://www.allfreedumps.com/SK0-005-dumps.html (470 New Questions)